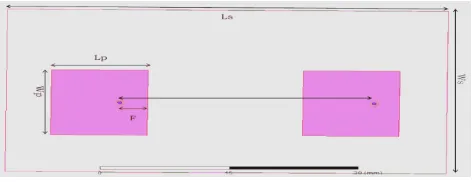
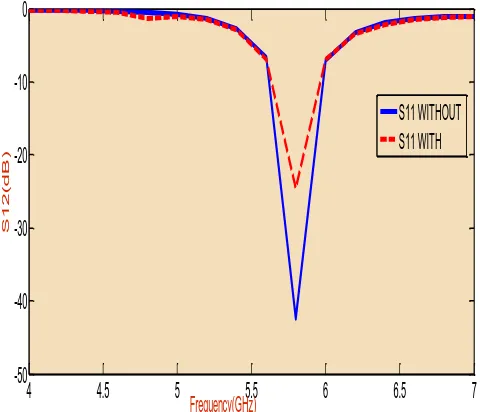
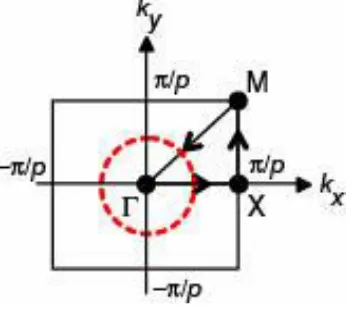
Minimization of Mutual Coupling in Arrays using Cross shape EBG
Full text
Figure
Related documents
KEYWORDS dinB ; Escherichia coli ; adaptive mutation; copy number variant; error-prone polymerase; gene ampli fi cation; lactose operon; local over- replication; mutagenesis; plasmid..
While the DSR protocol has a secure version ARIADNE [16], which employs symmetric key cryptography to provide security to the source routing process.. However,
If many loci are selected simultaneously, the strength of selection on a particular locus will tend to decrease over time (Chevin and Hospital 2008), rather than remain constant.
Inorder to make the informations more secure the secret message is hided in the image patch and the patch is reconstructed to produce a better embedded image.The hiding of
Based on the index and signatures, we propose an efficient two- phase pruning strategy including set similarity pruning and structure-based pruning, which utilizes the unique features
A city in which hard infrastructure and social infrastructure is fulfilled and the information and communication technology is used to deliver services remotely
In future, we will grow new strategies and calculations for finding continuous examples over information streams which beats the disadvantages of the existing
Teleost fish maintain a greater number of nuclear receptors (NRs) compared to other vertebrates due to a third genome duplication specific to their lineage (3R).. The retention