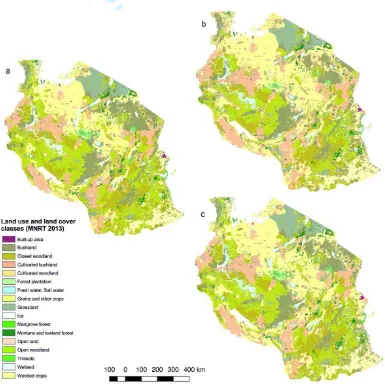
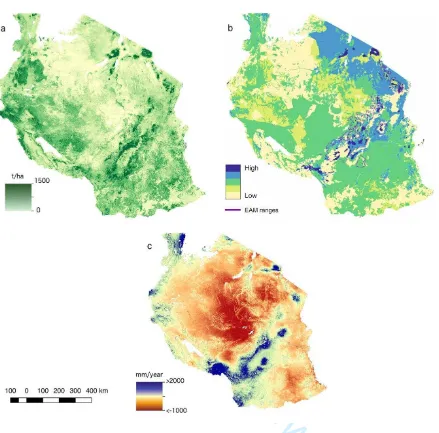
Scenarios of land use and land cover change and their multiple impacts on natural capital in Tanzania
Full text
Figure
Related documents
Intrusion detection is a set of techniques and methods that are used to detect suspicious activity both at the network and host level. Intrusion detection systems fall into two
A study of dielectric loss and dielectric constant of a sample as a function of frequency and temperature helps to understand the various polarization mechanisms
Synthesis of bimetallic nanoparticles is using inorganic layered materials which also predominantly role in stabilization as well as catalytically activity because of
3 the same surfaces as in the top left-hand panel except that this time the CMB surface was calculated using only the COBE , BOOMERANG (Antarctica flight) and MAXIMA-1 data. The
The fourth research question is concerned to examine how young people rate religion. as having a negative influence in
The 3D stack image module and the OpenGL rendering module are the core mod- ules of the program. They achieve the basic functionality of the program. The 3D stack image module
As part of the pro- cess of building a system to identify which visual features are salient and to describe them using nat- ural language expressions, we collected a corpus
a: Plasma renin concentration (PRC) of control (filtered air) and ultrafine carbon particles (UfCPs) exposed SHRs at several time points: before exposure (baseline), first, second