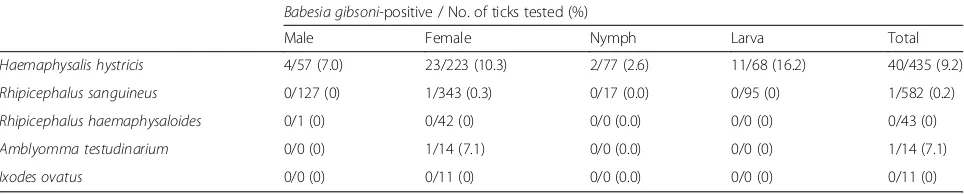
Molecular evidence for the transovarial passage of Babesia gibsoni in Haemaphysalis hystricis (Acari: Ixodidae) ticks from Taiwan: a novel vector for canine babesiosis
Full text
Figure


Related documents
In this work, the quality of the ground- water in the densestrice cropping area, Saraipali, Chhattisgarh, Central India is discussed1. The water is sodic in nature with extremely
We therefore focus on intrusion attacks and analyze what methods an attacker can use to read and write data from and to the ECUs.An attacker that wants to eject
In the model matching method of Sanathanan and Quinn (1987), frequency domain optimization is used to obtain a low-order approximate of the ideal controller given by the
According to the obtained information, the highest frequency between the basic themes in the analyzed sources is related to the content of the code (P10) called
MOMENTUM17 40 International Journal of Research in Advent Technology (IJRAT) Special Issue E ISSN 2321 9637 Sharadchandra Pawar college of Engineering, Dumbarwadi, Pune 410504,
Using the Connector/J JDBC driver, all sorts of Java applications can access a database and its data.. In the next chapter, we provide a comprehensive overview of the JDBC
Crude oil contains plenty of different ingredients and every ingredient has different steam pressure, dissolvability, viscosity and surface tension [1]. The group of
Hayden PW, Rudd TG, Dizmang D, et al: Evaluation of surgically treated hydrocephalus by radionuclide clearance studies of the cerebrospinal fluid shunt. Evans H, Thomas MD, Williams