Architectural Principles and Experimentation of Distributed High Performance Virtual Clusters
Full text
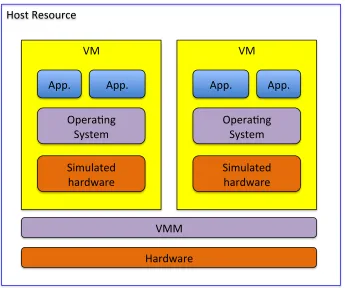
Figure
![Figure 1.1 Data analytics and computing ecosystem compared (from [25]),with virtualization included](https://thumb-us.123doks.com/thumbv2/123dok_us/8134743.243204/20.612.111.540.156.477/figure-data-analytics-computing-ecosystem-compared-virtualization-included.webp)

Related documents
If you copied/moved file from iPhone to iAccess using "Open in" function, the file will be copied to iPhone memory and stored in the app you opened it in to. To delete the
There are a ton of security methods for information protection that are acknowledged from the cloud computing suppliers, and they all give verification, secrecy,
Treatment with honey or metformin significantly lowered the increased blood glucose levels in diabetic compared to control non-diabetic rats (Table 1).. Combination
Completeness of learning ability of problem solving of student mathematics in class VII SMP HANG TUAH 2 Medan Year 2015/2016 academy on pocket discussion of flat wake with
Differences between previous study and academic success in first year anatomy and physiology, secondary school subjects and previous tertiary degrees were compared
National teams of students, who participated in 2012 Erasmus Intensive Program ‘Library, Information and Cultural Management – Academic Sum- mer School’ were asked to do researches
[r]
The initial UK proposals set out the legal claim that: “The 1951 Refugee Convention obliges states to provide protec- tion…There is no obligation under the 1951 Refugee Con- vention