Small modular reactors: A comprehensive overview of their economics and strategic aspects
Full text
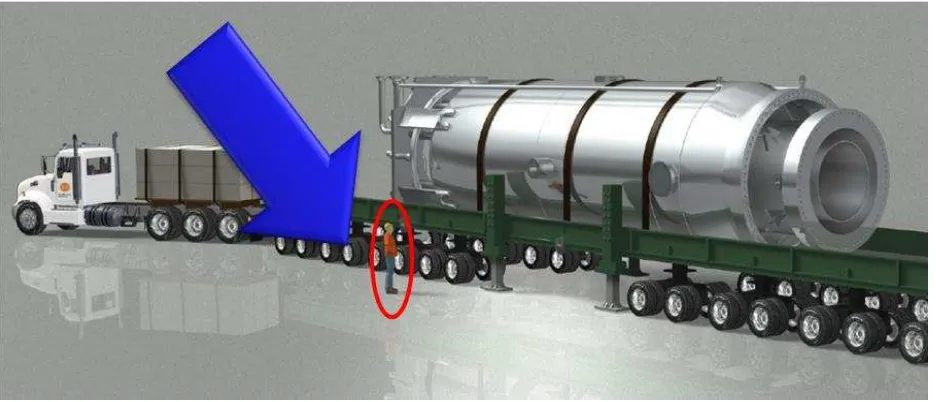
Figure

![Figure 3 (a) Parametric approach for estimating the capital cost of SMRs [23]](https://thumb-us.123doks.com/thumbv2/123dok_us/7945777.196425/16.612.65.454.420.628/figure-parametric-approach-estimating-capital-cost-smrs.webp)
Related documents
Technical Risk - Top Ten Checklist of Software Risks - Technical Risk Barry Boehm. Technical Risk - - Top Ten Checklist of Top Ten Checklist of
The information gain algorithm is used to select the most significant permissions, then the classification algorithms NaivBayes, Random Forest and J48 used to classify the
In order to achieve logistical excellence the manufacturing network is dependent on a thorough and powerful ICT strategy, with ICT systems (e.g. ERP-systems) that support
As a result, the basic principles and models identified cannot but be general, reflecting administration and management systems and also the countries’ concerns. There is
At the same time, one has to recognize the contextual as well as methodological differences between these educational surveys, particularly related to the item response models used,
This study focuses on four maintenance strategies such as Corrective Maintenance (CM), Predictive maintenance (PM), Time based preventive Maintenance (TM) &
The quanti- tative attributes of the mapped reservoir sand units were evaluated for porosity, water saturation, reservoirs net-to- gross and other petrophysical parameters..
Since seismic data is a reflection property, it only contains information regarding the change in rock properties from one lithological unit to another, as seen in the derivation

![Figure 6 Required temperature for industrial processes (adapted from[32])](https://thumb-us.123doks.com/thumbv2/123dok_us/7945777.196425/22.612.63.301.72.307/figure-required-temperature-industrial-processes-adapted.webp)