Vulnerability to abrupt climate change in Europe
Full text
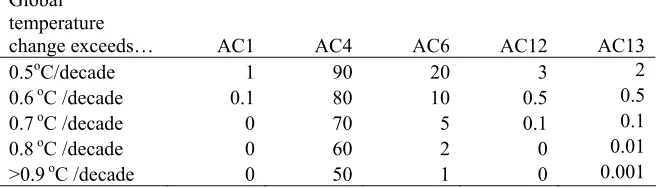
Figure




Related documents
Study #2: Behind the name: An Exploration of the Perspectives, Experiences and Behaviors Related to Social Identity, Self-Presentation and Social Penetration in Social
Mesebetsi ya Phumano ya Thepa e tsamaelanang le Mananeo a Merero ya Ditumellano tsa Tshireletso e tswela pele hantle, mme nakong ya selemo se fetileng dicorvette tsa paterole tsa
Складаючи власні схеми, учень навчається зчитувати схеми-коди; кодувати, схематизувати матеріал ( з об’ємного робити компактне). Своїми схемами
Kaustubh’s research interests lie in the areas of mobile systems and applications which involve Internet of Things (IoT), Smart Wearable Systems, Visible Light Communication,
During year 1 teaching in the resource room followed the usual Reading Recovery sequence of reading a familiar book, the teacher introducing a new book, reading a new book,
Rather than focusing exclusively on incentives and expectations about the base rate of errors, the field interview study examines payoffs of error detection more broadly by
The proposed method involves the following five phases: (i) generation of variable sized frequency subbands and bandpass filtering of raw EEG signals using these subbands, (ii)
This work has proposed blear blur technique for protecting the document images and it is compared with average blur, gaussian blur and motion blur.. We proposed dabber