Information systems audit and control issues with enterprise management systems: qualitative evidence
Full text
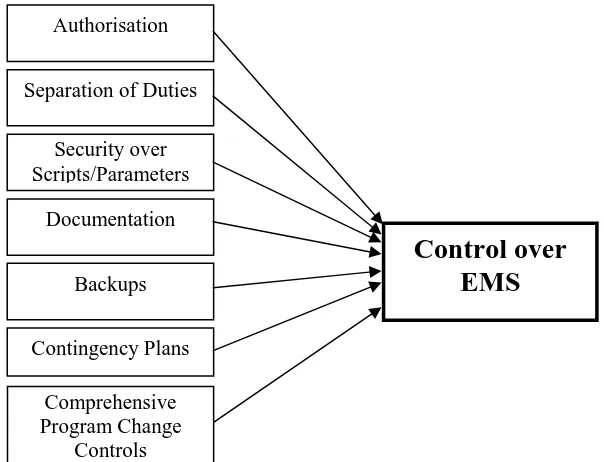
Figure
Related documents
Clifford, Clendenin, O'Hale & Jones, L.L.P... Manuel Louis Costa
• Performance for Film and TV • Staging Philosophy Year 3 • Professional Directions • Performance in Context • Professional Practice • Analysing Practice •
During 4 years of study students of the Faculty of International Economic Relations can get two higher professional education degrees – a degree of Financial University and a
ILFOBROM GALERIE GRADED FIBRE BASE PAPER …11. MULTIGRADE FB
This era of campus planning was strongly influenced by Clarence Stein’s Radburn model for urban development with its spatial segregation of pedestrians from
Academic Bachelor's programmes are based on scientific research and mainly prepare students for further studies at Master level. These degrees are awarded by universities and
• Although an employer may require a fitness for duty certification to address the employee’s ability to perform the essential functions of her job, it may do so only if the
Secondly, there is increasing attention to retrofit existing rolling stock having cast-iron block brakes with new block brake types (e.g. This will eventually reduce the aver-