An Efficient and Secured Framework for Mobile Cloud Computing
Full text
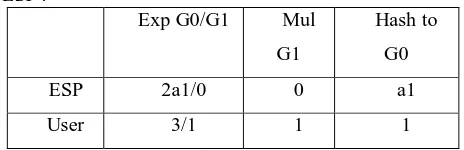
Figure
Related documents
Despite the increase in clinical crown height, a potential for pulpal exposure remains because tooth reduction is required to provide sufficient interocclusal space for crowns on
In the fifteenth century another great building, D, with its arcades opening up, on the ground floor, onto the courtyard, took up the whole of the western side of the Villa.. In
8 Attebery, like Irwin, distinguishes between the fantastic and fantasy: the fantastic as a mode of storytelling incorporates the whole of myth, fairy tale, magic realism,
Whilst all staff reported that facilities for hand hygiene were adequate, the observations and inventory identified that staff were not cleaning their hands as often as recommended
The purpose of the School of Graduate Studies at the University of Wisconsin-Platteville is to coordinate and oversee high quality, practitioner-oriented graduate programs whose
The survey assessed participants’ percep- tions of the magnitude of the faculty shortage, their in- terest in pursuing an academic career and teaching in various capacities,
Plastics producers and machinery builders are always pressed to lower production costs.By combining the understanding of these needs with Industry Leading control and
The figure also gives an indication of the types of policy and program responses girls’ diversity requires: broadly based social policies and systems such as those for