Engaging distance and on-campus students in problem based learning
Full text
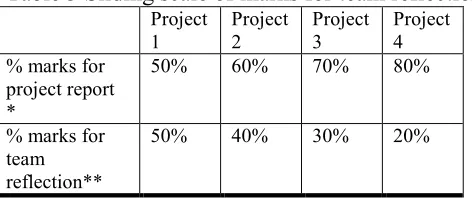
Figure



Related documents
Approaches of preserving privacy on databases can be divided into two categories: The first one for the data encryption, most approach using k-anonymity, the
COTLA and TOPIOCA, however, manage the vehicle flow sequence in the in- tersection using its surveillance system (the first-level sensors installed at the intersec- tion concerned
But even if returning Mexican families face barriers to school enrollment, should we expect the same association in Mexico between duration of residence and school enrollment
A new methodology and algorithm of constructing single and nested helical geometries are described in this paper. The problems faced during the model generation and meshing stages
: Non-sedation versus sedation with a daily wake-up trial in critically ill patients receiving mechanical ventilation (NONSEDA Trial): study protocol for a randomised controlled
The design has been the proposed full adder offered 21.57% change regarding the past plan as far as Power Consumption (90-nm technology at 1.2 V).. Relating Power change was
the tool pose, tool overhang length, rigidity of the machine transmission parts, workpiece stiffness characteristics,. and ultimately establish a general stiffness modelof