External memory priority queues with decrease-key and applications to graph algorithms
Full text
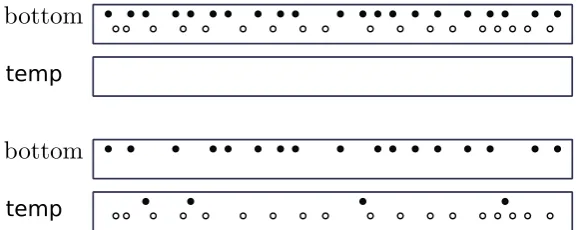
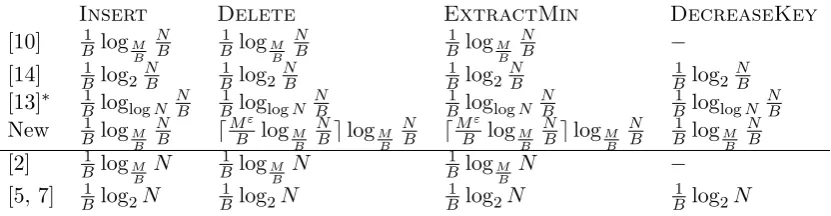
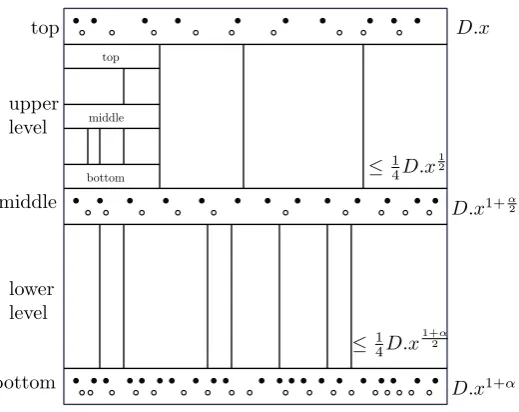
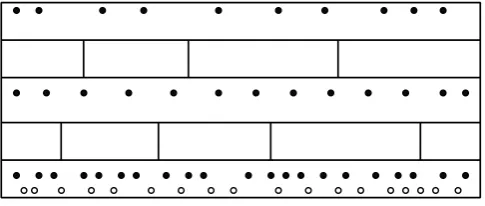
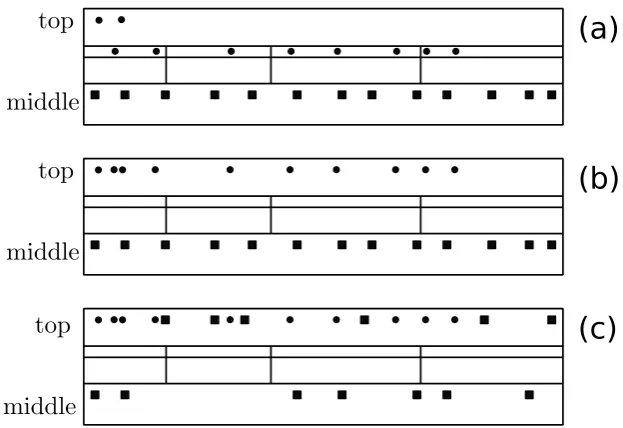
Figure
Related documents
Input: positive set P , reliable negative set RN , number of features N to be considered to build the recommender, choice CH to specify the method to be used in second step to build
14 When black, Latina, and white women like Sandy and June organized wedding ceremonies, they “imagine[d] a world ordered by love, by a radical embrace of difference.”
We have presented and validated a simplicial branch and duality bound algorithm for globally solving the sum of convex–convex ratios problem with nonconvex feasible region..
Note that Reserve words (Verilog commands and keywords) may not be used as identifiers: always and assign attribute begin buf bufif0 bufif1 case casex casez cmos deassign
ERISA furthers its objectives in part through designating as a fiduciary any financial professional who provides investment advice to retirement investors about
The pro- posed method is implemented in a two-dimensional case and three different cylindrical cloaks are considered in our simulations: the ideal cloak, the simplified cloak based
harvested site at SW 170° to SE 230° (Unpublished data, Annalea Lohila, Finnish Meteorological Institute Helsinki). The differences in above ground autotrophic
Different kind of biomass waste are used as feedstock for anaerobic digestion: various type of kitchen waste, organic fraction of municipal solid waste, animal