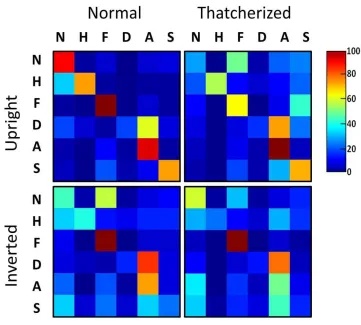
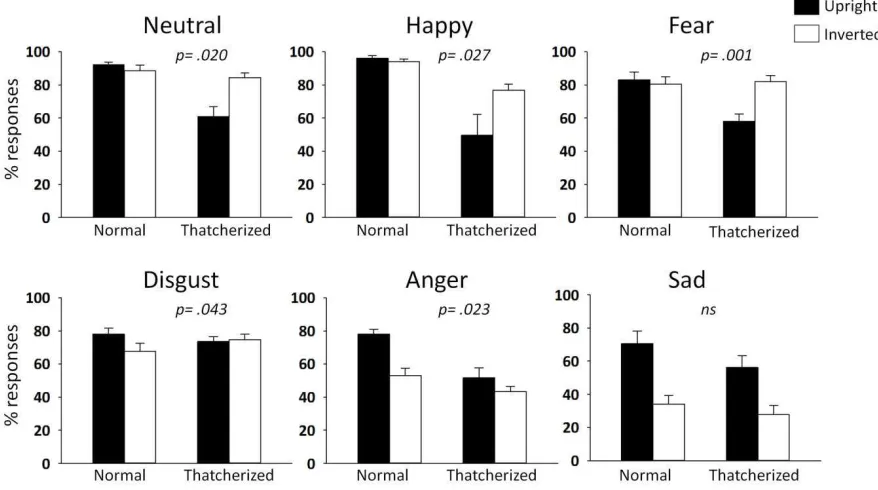
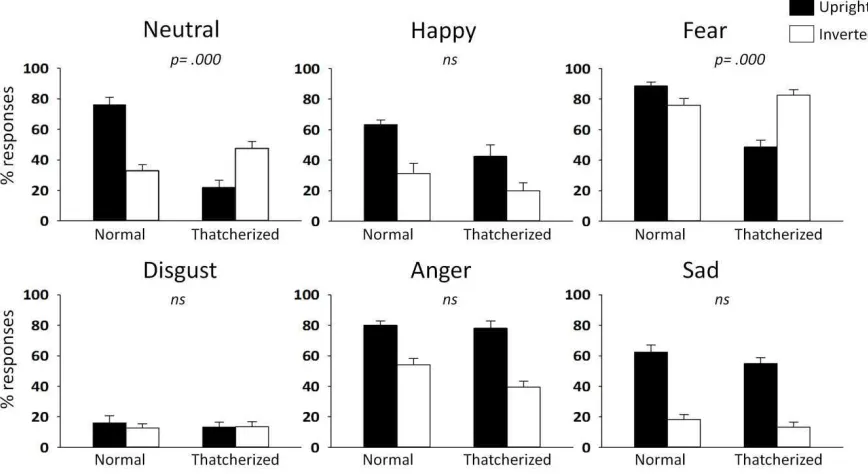
Inversion improves the recognition of facial expression in thatcherized images
Full text
Figure


Related documents
Senior executives from Cases One and Two, both Johannesburg Stock Exchange (JSE) listed minerals and metals producers, represented companies highly dependent on both FDI and a
Finally, we also mention a companion paper [29], in which we study problems Identifying Code, Locating-Dominating-Set, Open Locating-Dominating Set and Metric Dimension on interval
In this section, we give an overview of our framework for establishing the relation between a CSP specification and a low-level implementation. We assume that a CSP specification
HKIA has incorporated a strong framework within IATA but in line with its leading status as the world’s largest airfreight hub, HKIA needs to continue to strive to reach higher
Other Private Cloud Use Cases Online Gaming Cost / Control / Concurrency Amazon environment Millions of users / Massive concurrency Booting 100s of VMs Service Provider
Such a negative correlation between changes in anticipated (exogenous) …scal variables stems …rstly from the temporary nature of some policy measures: their budget impact is felt
This model is also used in the basic DP functions for cyclic data transmission where each module has a constant number of input and/or output bytes which are transmitted in a
Thus, in the cyber context, to attribute adverse cyber operations to a State, the injured State must establish the following facts: (1) the identity of the person, group of