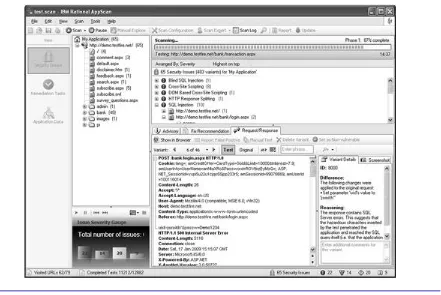
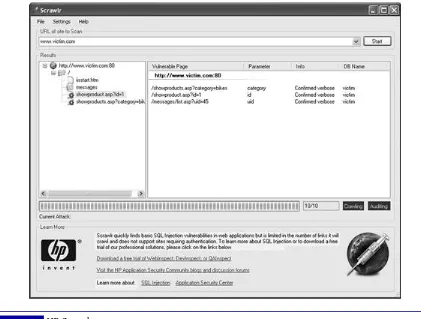
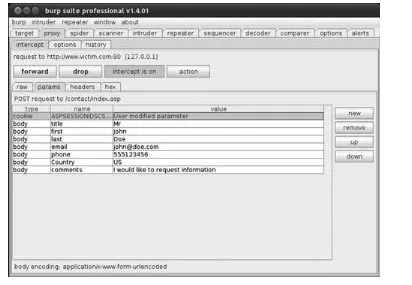
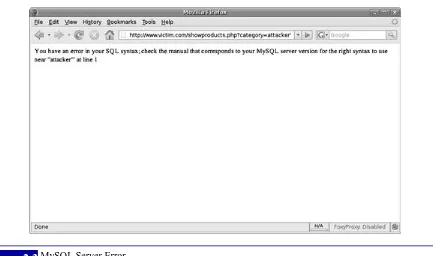
SQL Injection Attacks and Defense pdf
Full text
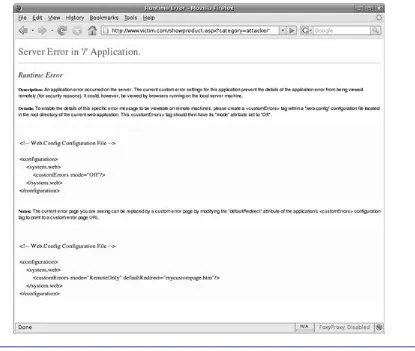
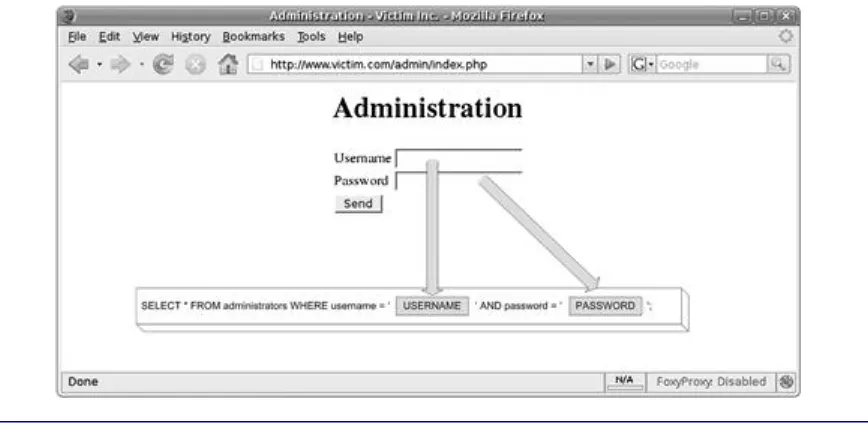
Figure
Related documents
“Prequalification document for EPC”, in relation to the pre-qualification of companies for Engineering Procurement and Construction (EPC) of the Iran Pakistan Gas Pipeline Project,
There were differences by top source country with 94 per cent of Essential Skills workers from India gaining residence as a principal skilled migrant compared with 89 per cent
Considering the increasing number of potential Internet users in China, the possibility of current E-commerce platforms, and the uniqueness of the E-commerce solution in China,
In this chapter, I shift from thinking about habit in relation to mid-century literary allusion and textuality to analyzing the relationship between Wilkie Collins’s unconscious
In healthy individuals, listening to pain cries has been reported to elicit functional activation within the pain matrix of the brain, so several studies have used this task to
Title: Elevated Body Mass Index is associated with reduced integration of sensory-driven with internally-guided resting-state functional brain networks.. Authors:
was also seen for deeper dipoles although it is somewhat less pronounced, with OPMs still out- performing SQUIDs up to approximately a 25% error on the forward field. Whilst
En el escenario futuro, el modelo no proyecta eventos extremos de temperatura por debajo de 0 o C para el área 3, restringiendo la incursión de la isoterma de 0 o C a latitudes más