Security policy and data protection awareness of mobile devices in relation to employees’ trusting beliefs
Full text
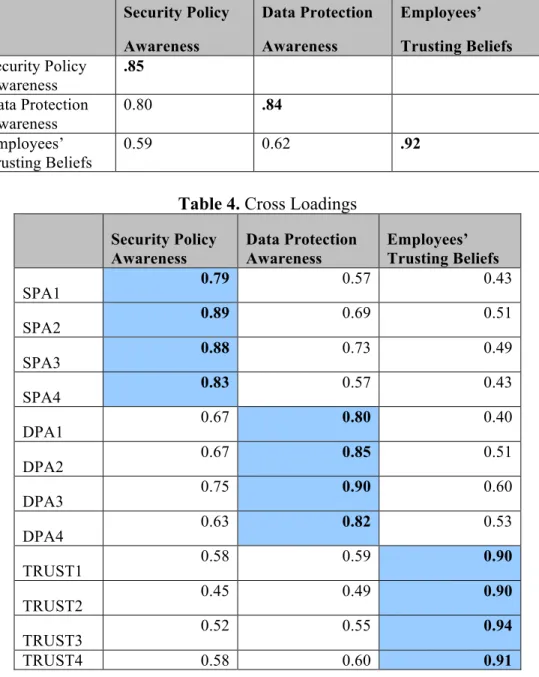
Figure
Related documents
Policy Name: IT and Mobil e Devices Security Policy Policy No: P04002 Approved Date: May 2014 Review Date: May 2016 Approved by: Senior Management Team EqIA Completed:
To protect Legal Aid NSW information, once approved for access to the Legal Aid NSW network, personally owned mobile devices cannot be shared with or loaned
This would essentially involve appointing national politicians to take up part-time roles in Brussels/Strasbourg rather than directly elected MEPs, much in the same way that
It may also be possible to shelter some or all of the gain from the deemed disposition or estate freeze using the $750,000 lifetime capital gains exemption for qualified
- February 28, 2011 EMC Corporation and IBM Corporation today announced the extension of a technology licensing agreement that enables customers to install and utilize EMC and IBM
tuberculosis infection promotes adipose tissue in flammation To investigate the involvement of the tissues linked to glucose and lipid metabolism and the progression towards
An MDM solution is intended to provide centralized security and management of mobile devices in order to protect corporate data stored on the devices, and data that these devices
Even still, modern copper cabling’s carrying capacity horizon (how much more bandwidth we can get out of copper as opposed to fiber) is much much closer than fiber. While we are at