Size and shape analysis of error prone shape data
Full text
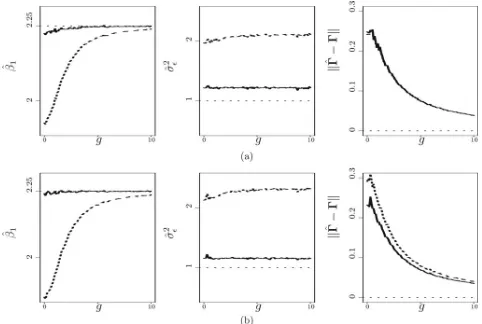
Figure

Related documents
Assume RPKI-RTR RPKI Engine Repository Mgt Publication Protocol RCynic Gatherer to Rtr RPKI Protocol BGP Decision Process Cache django RPKI Repo... Origin Validation
Kho du lieu duqc xay dung de tien loi cho viec truy cap theo nhieu nguon, nhieu kieu du lieu khac nhau sao cho co the ket hop duqc ca nhung ung dung cua cac cong nghe hien dai va
Unpaired-t-test was used to compare the written test score of the students taught using these interactive, participatory sessions and the traditional training.. Approval was
The partial charges on the hydrogen atoms participating in the proton conduction process were computed for the system shown in Figure 30 from the Density Derived Electrostatic
This study aims to determine the effect of administration of State Property, which consists of bookkeeping, inventory, and reporting on the optimization of fixed assets
As described in the section Production of recombinant antibody fragments by Escherichia coli , this micro-organ- ism has shown to be a potential expression host for anti-
Abstract— This paper explores the potential of wireless power transfer (WPT) in massive multiple-input multiple- output (MIMO)-aided heterogeneous networks (HetNets), where massive
The objec- tives were to explore the factor structure and internal reliability of the scale, the extent to which the scale discriminates between primary care practices (discrim-