Review of practice led research in art, design & architecture
Full text
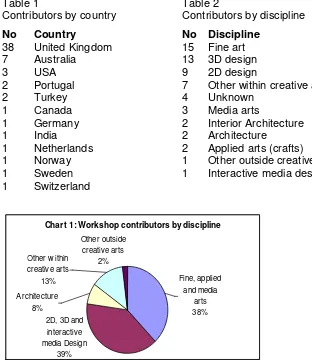
Figure



Related documents
A small weakness in F-Secure Mobile Security is that this service is not activated by default, and that the user is not actively encouraged to set it up, meaning that if the phone
Out of the nineteen articles received from the contributors and positively assessed by an international assessors' team to be published in this volume, four are concerned
The Structural Mechanics calculations were based on the ‘force method’ that has been widely used in mechanical engineering since the early days of the field of strength of
For nonideal systems, but for systems with nearly rigid bodies whose geometry does not change significantly during the application of the forces, we may still replace the forces by
Based on the simulation results, the suggested tuning method is capable to reduce the liquid slosh level in the same time produces fast input tracking of the tank without
Such approaches described in this paper are Routing Switch, High Performance Routing, Gigabit Routers, and I/O Switching. However, it is important to note that these
This SOP applies to all personnel, substitutes, and volunteers in Child, Youth and School Services center-based programs (CYSS) and CYSS regulated activities, including but not
Results from the analysis were compared with estimates for the incidence of liver cancer, after accounting for liver cancer under-report- ing, cancer morphology (HCC), and the