Blind Modulation Recognition in Wireless MC CDMA Systems Using a Support Vector Machine Classifier
Full text
Figure

Related documents
Research has been conducted in the South–West of Nigeria to determine the awareness level of secondary school students on quantity surveyors’ roles in the Nigerian
In this paper, the morphological and histological structure of the wings of two species of beetles, Tribolium castaneum and Tribolium confusum, has been investigated using
From one-port parameters, which were collected using a short load, the impedance values of lumped elements are obtained, and the quality factor and SRF of the lumped elements
This study was meant to address the issue of health insurance penetration, especially by the National Hospital Insurance Fund), among the low income groups of the society in Kenya..
The Advanced Encryption Standard (AES) techniques is used to provide the security services and the Discrete Wavelet Transform (DWT) and Discrete Cosine Transform (DCT)
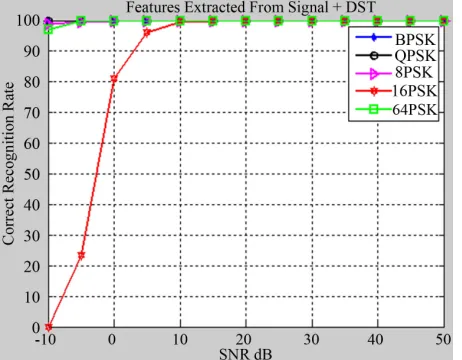
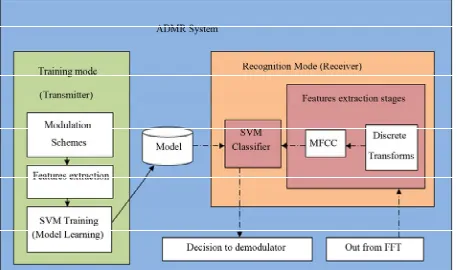
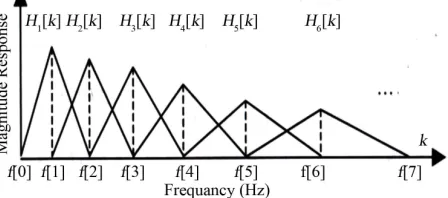
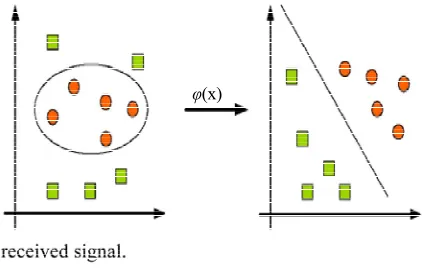
Among deterministic approaches Discrete Cosine Transform (DCT) [8], [9], Discrete Fourier Transform (DFT) [10], and Discrete Wavelet Transform (DWT) [11] are the
Evans, Nicole M., "The Process of Exercise Participation in the Community for Functional Recovery Post Formal Rehabilitation among Survivors of Stroke: a grounded theory
Dominion’s Democracy Suite is a robust and secure Election Management System (EMS) that is used to design and set up an election, as well as tally and report the results of