How To Authenticate On An Xtma On A Pc Or Mac Or Ipad (For A Mac) On A Network With A Password Protected (For An Ipad) On An Ipa Or Ipa (For Mac) With A Log
Full text
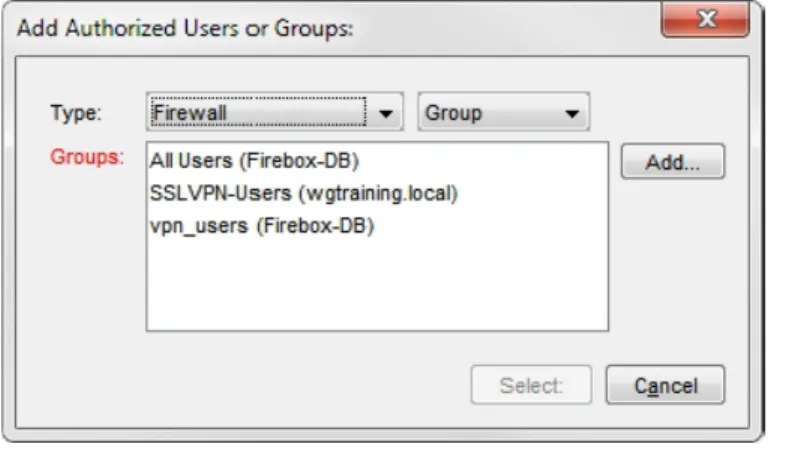
Figure

Related documents
Type Inherit Flag Access Mask Object Type Inherited Object Type Specify this ACE is for ALLOW/DENY purposes Specify how this ace should be inherited A mask to specify what kind
Member, Director of Special Education Search Committee, Burlington School District, Spring 2015. Member, Family School Partnership Team, Partnership for Change: Nellie Mae Grant,
All users that match the particular skills and attributes defined under the selected search name will now be displayed in the Search Result screen. The ID and Name columns
You should create a configuration that uses external FPolicy servers when you want to do such things as monitor and record file access events, provide quota services, perform
Further, when a cash value policy is bought by a transferee, upon a later sale to a third party, any gain up to the policy’s cash surrender value will be taxed as ordinary income..
Moreover, the urban-to-urban migrants are a better comparison group for the rural-to-urban migrants than urban local residents because they are both “outsiders.” Rural-to-urban
improves over its myopic and deterministic counterpart (SMS-EMOA) by providing internal predictive and estimation Bayesian models to track time-varying decision and objective
to the license agreement, and then, click Next. On the Initialization Code page, in the Initialization Code box, enter your initialization code that you previously recorded and