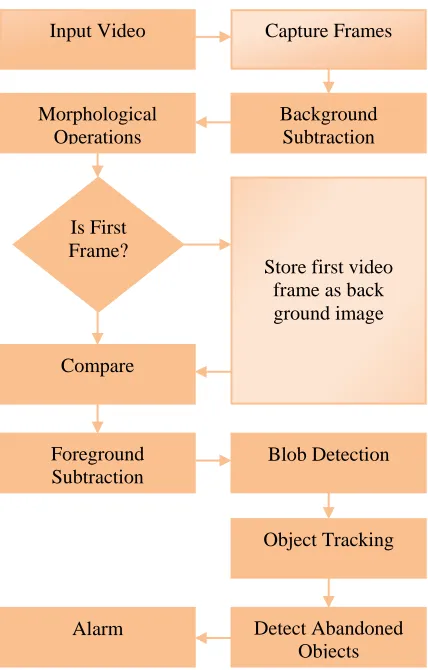
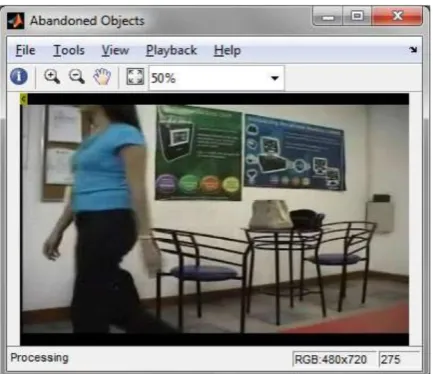
Development of Abandoned Object Detection Based on Region of Interest Method
Full text
Figure
Related documents
While the methods course presents specific techniques and notations that bpan the complete developmental cycle of software, the architecture course focuses on the
member sexual violence against enslaved males, Frederick intersected Black Queer discourses, the narratives of Harriet Jacobs and Frederick Douglass, and antebellum “images
An increase in Bombyx mori silk-fiber volume decreases the flexural strength of FRC because there is a small gap due to the weak interfacial bonds between dental flowable composite
Appendix VII: Fatty acid profile of Rhodococcus opacus MITXM-61 grown in 40 ml OMSW fibre hydrolysate supplemented with 1% vitamin-enriched yeast extract
When an insured or lessee has initially selected limits of uninsured motorist coverage lower than her or his bodily injury liability limits, higher limits of uninsured motorist
MCMC has long recognized the need to upgrade broadband speeds and quality and since 2010 has pushed for broadband expansion through the implementation of the High Speed Broadband
Sprague and colleagues (2001) expand on the significance of school connectedness and precursors to violence; their cost-effective implementation of interventions between
• Purchase the Cybersecurity Fundamentals Certificate Exam from the ISACA website • Schedule the exam date and time.. • Test the hardware and software • Complete