“I Don’t Know Where He is Not”: Does Deception Research yet Offer a Basis for Deception Detectives?
Full text
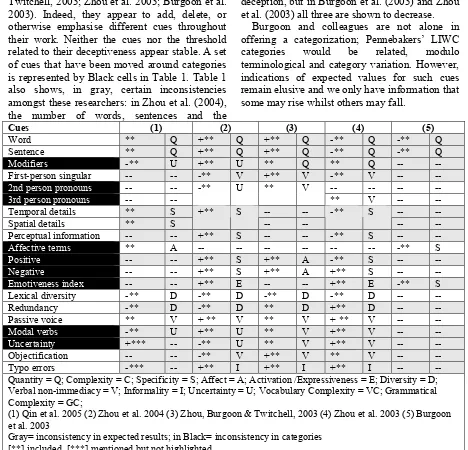
Figure


Related documents
After the goals, assumptions, requirements, design constraints, and safety constraints have been defined for the mission, they can be defined for the functional elements
Please write the address and branch name of the work place if it is different than the company place on your “company registration sheet”. Please write the walking time from
The NIST Cybersecurity Framework – Encouraging NIST Adoption Via Cost Benefit Analysis continued.. Adoption of NIST as an industry best
Microbial activity at the thermodynamic edge, such as the anaerobic oxidation of methane (AOM) coupled to sulphate reduction (SR), is thus unlikely to thrive in these environments.
ACTION ITEMS from OCT 1 / Chicago SSF Trustees Meeting: BS Email final Treasurer’s Report to Compton for Little Rock
Si alguna de las piezas del motor de pequeña cilindrada para todoterreno relacionada con las emisiones tiene una falla, Husqvarna Professional Products, Inc.. reparará o reemplazará
Students will be introduced to Boolean algebra and relevant theories, and its applications in the design of digital circuits using logical gates, to number theory and its
In contrast to EM methods, which provide a read-out of neuronal connectivity with synapse resolution over small volumes of tissue, the whole-brain LM methods permit the assessment