International Journal of Scientific Research in Computer Science, Engineering and Information Technology © 2018 IJSRCSEIT | Volume 3 | Issue 1 | ISSN : 2456-3307
Achieving Secured Group Data Sharing Using Key Aggregate
Searchable Encryption
P. Rupini
1, Mohammed Alisha
2, Dr. D. Mohan Reddy
31PG Scholar, Dept. of Computer Science and Engineering, Amalapuram Institute of Management Sciences and College of Engineering, Mummidivaram, East Godavari District, Andhra Pradesh, India
2Associate Professor& Head of the Department, Computer Science and Engineering, Amalapuram Institute of Management Sciences and College of Engineering, Mummidivaram, East Godavari District, Andhra Pradesh,
India
3Professor & Principal, Amalapuram Institute of Management Sciences and College of Engineering, Mummidivaram, East Godavari District, Andhra Pradesh, India
ABSTRACT
Data sharing is a critical usefulness in cloud storage. In this article, we portray the method for safely, effectively, and adaptable share Data with others in cloud storage. We portray new public key cryptosystems which create steady size cipher texts with the end goal that effective designation of decryption rights for any arrangement of cipher texts are conceivable. The oddity is that one can total any arrangement of secret keys and make them as conservative as a single key, however including the energy of all the keys being collected. As it were, the secret key holder can discharge a steady size total key for adaptable decisions of figure content set in cloud storage; however the other encrypted documents outside the set stay secret. This minimized total key can be helpfully sent to others or put away in a keen card with extremely constrained secure stockpiling. We give formal security investigation of our plans in the standard model. We likewise depict other utilization of our plans. Specifically, our plans give the primary public key patient-controlled encryption for flexible hierarchy, which was yet to be known.
Keywords : cryptosystem, encryption, cloud storage, public key, SHA algorithm, cipher text, drop box.
I.
INTRODUCTION
Cloud storage has developed as a promising taking care of an issue for giving universal, helpful, and on-request gets to a lot of Data shared over the Internet. These days, a large number of clients are sharing individual Data, for example, photographs and recordings, with their companions through a devoted site or other application which empowers clients to speak with every last other by posting data, messages, and pictures in view of cloud storage once a day. Business clients are likewise being pulled in by cloud
being spilled in iCloud). To deliver clients identify with ensure potential Data spills in cloud storage; a prevalent way of managing a circumstance is for the Data proprietor to encrypt every one of the Data before transfer to cloud.
II.
MATERIALS AND METHODS
The best solution for the above problem is that Alice encrypts files with distinct public-keys, but only sends Bob a single (constant-size) decryption key.. Since the decryption key ought to be sent by means of a safe channel and kept secret, little key size is constantly attractive. For instance, we can't expect expansive capacity for decryption keys in the asset limitation gadgets like advanced mobile phones, savvy cards or remote sensor hubs. Particularly, these secret keys are normally put away in the carefully designed memory, which is generally costly. The present research endeavors mainly focus on limiting the correspondence prerequisites, (for example, data transmission, rounds of correspondence) like total mark. Be that as it may, very little has been done about the key itself.
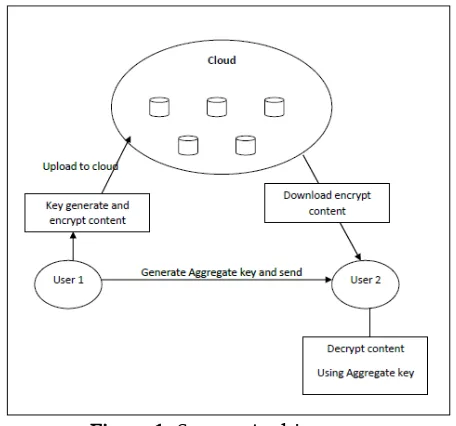
Figure 1: System Architecture
Benefits of Proposed System
It is more secure. Decryption key should be sent via a secure channel and kept secret. It is an efficient public-key encryption scheme which supports flexible delegation.
III.
METHODOLOGY MODULES
Access control: Access control is method for constraining access to a framework or to physical or virtual assets. In registering, get to control is a procedure by which clients are conceded get to and certain benefits to frameworks, assets or data .In get to control frameworks, clients must present accreditations previously they can be allowed get to. In physical frameworks, these qualifications may come in many structures; however certifications that can't be exchanged give the most security. It stipends validated clients access to particular assets in view of access approaches and the authorization level doled out to the client or client gathering. Access control
regularly incorporates confirmation, which
demonstrates the personality of the client or customer machine endeavoring to get to the records. After the introduction of the models identified with get to control in plaintext and encrypted database, we portray how Mute DB changes an entrance control framework for the plaintext model to a grid reasonable for the scrambled database, and how it creates client qualifications. Give R a chance to be the arrangement of assets that speak to plain content occupant Data, S the arrangement of plaintext database structures, E the arrangement of encrypted inhabitant Data, U the arrangement of clients, and K the arrangement of encryption keys. We characterize An as the entrance control lattice where, for every client u P U and for each structure s P S, there exists a paired approval decide a that characterizes whether an entrance to s by u is denied or permitted.
Encrypted Database Model: Database encryption is the way toward changing over Data, inside a database, in plaintext arrange into futile figure message by the methods for a reasonable algorithm. Database decryption is changing over the futile figure content into the first data utilizing keys created by the encryption algorithms. Database encryption is given at the document or segment level. Encryption of a database is expensive and requires more storage room than the first Data. The means in scrambling a database are: Determine the criticality of the requirement for encryption, figure out what Data should be encrypted, and figure out which
algorithms best suit the encryption standard, Determine how the keys will be overseen. Various algorithms are utilized for encryption. These algorithms produce keys identified with the encrypted Data. These keys set a connection between the encryption and decryption strategies. The scrambled Data can be unscrambled just by utilizing these keys. Scrambled Data is contained in encrypted tables put away in cloud database servers. For each plaintext table, the Mute DB DBA customer creates the comparing encrypted table and an interesting encryption key. The name of the encrypted table is figured by scrambling the name of the plaintext table through that key. The encryption algorithm utilized for scrambling the table names is a standard AES algorithm in a deterministic mode (e.g., CBC with consistent introduction vector). In such a way, just the clients that know the plaintext table name and the comparing encryption key can process the name of the scrambled table. The deterministic plan is favored on the grounds that it permits a correspondence amongst plaintext and encrypted tables and enhances the productivity of the inquiry interpretation process.
Data Group Sharing Server can utilize this total trapdoor and some public data to perform catchphrase pursuit and restore the outcome to Bob. Along these lines, in KASE, the appointment of catchphrase look right can be accomplished by sharing the single total key. We take note of that the
appointment of decryption rights can be
who approaches at any given time. Notwithstanding the cloud Data protection laws featured underneath, many ventures need to likewise stick to arrangement. Cloud Storage Cloud storage is a model of Data stockpiling where the advanced Data is put away in legitimate pools, the physical stockpiling traverses various servers (and frequently areas), and the physical condition is ordinarily possessed and overseen by a facilitating organization. These cloud storage suppliers are in charge of keeping the Data accessible and public, and the physical condition ensured and running. Individuals and associations purchase or rent stockpiling limit from the suppliers to store client, association, or application Data. Cloud storage administrations might be gotten to through an arranged cloud PC benefit, a web benefit application programming interface (API) or by applications that use the API, for example, cloud work area stockpiling, a cloud storage portal or Web-based substance administration frameworks
IV.
Conclusion
Considering the pragmatic issue of protection safeguarding Data sharing framework in view of public cloud storage which requires an Data proprietor to disperse an extensive number of keys to clients to empower them to get to his/her archives, we out of the blue propose the idea of key-aggregate searchable encryption (KASE) and develop a solid KASE conspire. Both examination and assessment comes about affirm that our work can give a successful answer for building down to earth Data sharing framework in view of public cloud storage. In a KASE conspire, the proprietor just needs to appropriate a solitary key to a client when imparting bunches of archives to the client and the client just needs to present a solitary trapdoor when he inquiries over all records shared by a similar proprietor. Be that as it may, if a client needs to inquiry over records shared by numerous proprietors, he should produce different trapdoors to the cloud. The most effective method to lessen the quantity of trapdoors under multi-proprietors setting is a future
work. Besides, combined clouds have pulled in a great deal of consideration these days; however our KASE can't be connected for this situation straightforwardly. It is likewise a future work to give the answer for KASE on account of united clouds.
V.
REFERENCES
[1]. C. Dong, G. Russello, N. Dulay. "Shared and searchable encrypted data for untrusted servers", Journal of Computer Security, pp. 367-397, 2011.
[2]. F. Zhao, T. Nishide, K. Sakurai. Multi-User Keyword Search Scheme for Secure Data Sharing with Fine-Grained Access Control. Data Security and Cryptology, LNCS, pp. 406-418, 2012.
[3]. J. W. Li, J. Li, X. F. Chen, et al. "Efficient Keyword Search over Encrypted Data with Fine-Grained Access Control in Hybrid Cloud", In: Network and System Security 2012, LNCS, pp. 490- 502, 2012.
[4]. J. Li, K. Kim. "Hidden attribute-based signatures without anonymity revocation", Data Sciences, 180(9): 1681-1689, Elsevier, 2010.
[5]. X.F. Chen, J. Li, X.Y. Huang, J.W. Li, Y. Xiang.
"Secure Outsourced Attribute-based
Signatures", IEEE Trans. on Parallel and Cloud
Systems, DOI.ieeecomputer-society.org
/10.1109/TPDS.2013.180, 2013.
[6]. J.Li, X.F. Chen, M.Q. Li, J.W. Li, P. Lee, Wenjing Lou. "Secure Deduplication with Efficient and Reliable Convergent Key Management", IEEE Transactions on Parallel and Cloud Systems, 25(6): 1615-1625, 2014. [7]. Z. Liu, Z. Wang, X. Cheng, et al. "Multi-user
Searchable Encryption with Coarser-Grained Access Control in Hybrid Cloud", Fourth
International Conference on Emerging
Intelligent Data and Web Technologies (EIDWT), IEEE, pp. 249-255, 2013.
Storage Security in Cloud Computing", Proc. IEEE INFOCOM, pp. 525-533, 2010.
[9]. S. Yu, C. Wang, K. Ren, and W. Lou, "Achieving Secure, Scalable, and Fine-Grained
Data Access Control in Cloud
Computing",Proc. IEEE INFOCOM, pp. 534-542, 2010.
[10]. R. Lu, X. Lin, X. Liang, and X. Shen, "Secure Provenance:The Essential of Bread and Butter of Data Forensics in Cloud Computing", Proc. ACM Symp. Data, Computer and Comm. Security, pp. 282-292, 2010
[11]. X. Song, D.Wagner, A. Perrig. "Practical techniques for searches on encrypted data", IEEE Symposium on Security and Privacy,IEEE Press, pp. 44C55, 2000.
[12]. R. Curtmola, J. Garay, S. Kamara, R. Ostrovsky. "Searchable symmetric encryption: improved definitions and efficient constructions", In: Proceedings of the 13th ACM conference on Computer and Communications Security, ACM Press, pp. 79-88, 2006.
[13]. S. Kamara, C. Papamanthou, T. Roeder. "Dynamic searchable symmetric encryption", Proceedings of the 2012 ACM conference on Computer and communications security (CCS), ACM, pp. 965-976, 2012.
[14]. D.Boneh, C. G, R. Ostrovsky, G. Persiano. "Public Key Encryption with Keyword Search", EUROCRYPT 2004, pp. 506C522,2004..
[15]. Z. Liu, Z. Wang, X. Cheng, et al. "Multi-user Searchable Encryption with Coarser-Grained Access Control in Hybrid Cloud", Fourth
International Conference on Emerging
Intelligent Data and Web Technologies (EIDWT), IEEE, pp. 249-255, 2013.
ABOUT AUTHORS:
P.RUPINI is currently
pursuing her M.Tech
Computer Science &
Engineerin at Amalapuram
Institute of Management
Sciences and College of
Engineering.
MOHAMMED ALISHA is
currently working as a
Associate Professor and
Heading the Department of
Computer Science and
Engineering at Amalapuram
Institute of Management
Sciences and College of Engineering, Mummidivaram. He is a Post Graduate in Computer Science and Engineering and had 12 years of Experience. His Research interests include Spatial Data Mining, Web Designing, Java Programming, Computer Networks and Data Warehousing.
Dr. D. MOHAN REDDY
received the B.Tech. Degree
from Jawaharlal Nehru
Technological University,
Hyderabad, India and he