A26 5836 0 IBM 1621 Paper Tape Unit pdf
Full text
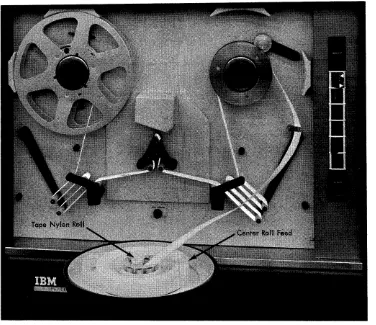
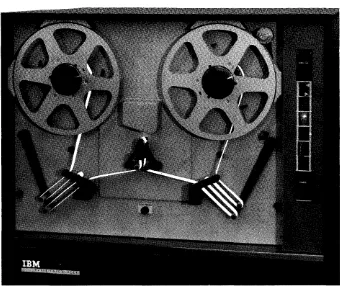
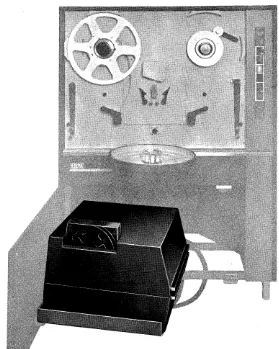
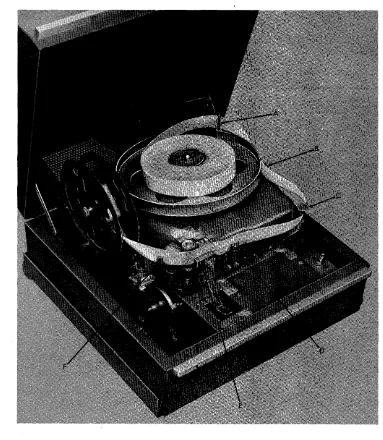
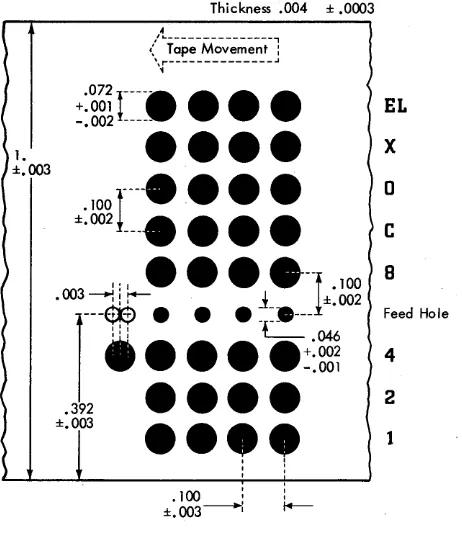
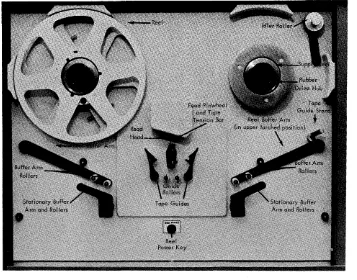
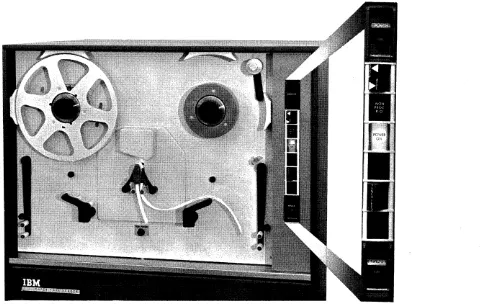
Figure
Related documents
Virtual system progresses, for example, Virtual Private Network (VPN), support clients with a modified network environment to get Cloud resources. Virtualization techniques are
Natural Language processing (NLP) [7] and Information Extraction (IE) [7][8] are the most popularly used techniques for text mining. There are other techniques that can be
Berdasarkan tabel penelitian relevan di atas maka dapat diketahui bahwa dalam penggunaan dana BOS yang dilakukan oleh sekolah-sekolah sudah sesuai dengan keinginan semua
Pembelajaran kooperatif adalah suatu model pembelajaran yang menggunakan kelompok kecil, setiap siswa yang ada dalam kelompok mempunyai tingkat kemampuan yang
The case study also used official statistical data on information technologies application, educational acts and decrees of the President of the Republic of Kazakhstan
We show that En1 induces Nurr1 target genes during development (including Th, Dat and Ahd2) in a rostrolateral subset of mdDA neurons, and that absence of En1 results in similar
This is a mandatory question (required), so that it is expected that it will be fulfilled. Secondly, currently, there is no support for the first- line in handling the
Login Data Page after login process is shown Username login and password can be filled in the edit box field, as expected Accepted Click on Website Content