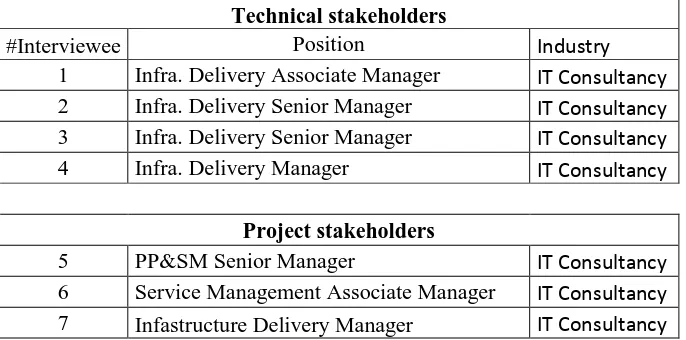
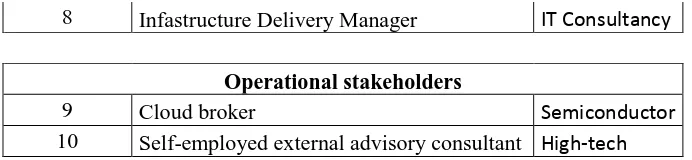
Managing the organizational transition towards cloud computing
Full text
Figure
Outline
Related documents
The Subway Operator The Security Service Provider The Tenant System Mgmt CloudCorp The Cloud Mgmt Provider TenSys The Telecom Operator.. Key Objectives Legal Guidance on Data
The analysis not only provided insights into scaffold diversity of the PubChem Compound database, but also enables scaffold-based hierarchical visualization of user compound data
Using DNA and amino acid sequences in molecular systematics has several advantages over traditional morphological approaches [6]: the universality of the character types and
F. Time of day for providing PMTCT services : Increased male participation in VCT and couple testing occurred in Kinshasa when the MCH.. Most health facilities offer these services
Our data indicated that among patients admitted to an OU for skin and soft tissue infections, women and patients with a leukocytosis of greater than 15,000 were more likely to
The aims of this systematic literature review were to provide an overview of the existing cross-European stud- ies on sedentary time in adults, to describe the variation in
Immunohistochemical staining for follicular dendritic cell immunoarchitectural patterns (FDC patterns) in small B cell lymphoma (SBL) specimens; differences in staining
Out of the antioxidant enzymes studied the activity of Peroxidase was highest in mature leaves of Ageratum and Catalase in root of Tridax.. KEYWORDS: Asteraceae