Thinking In Java Second Edition pdf
Full text
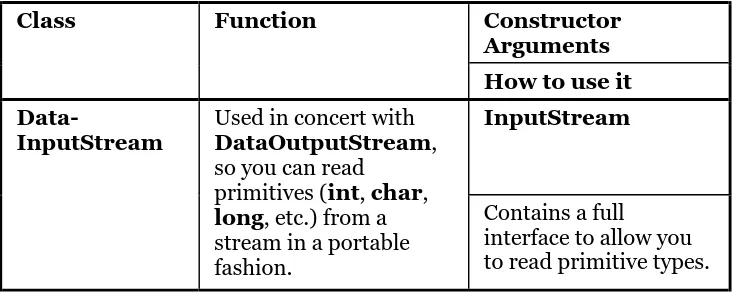
Figure
Related documents
In examining each figure, we will explore three basic topics for each major figure: the philosopher’s theory of the nature of knowledge; the implications of this theory for
In a 2012 case, in the context of a bitter orthopaedic dispute, the defendant’s orthopaedic expert, Mr Ved Goswami, attempted (for the first time in the joint statement) to deal
Our contri- butions are as follow: (i) we present a large scale measurement study of the malware threatening users residential networks, (ii) we identify hidden yet malicious
The hypothesis put forward with respect to the XLPE insulated cables is that degradation of field aged cables can be detected applying chemical analyses and electrical
A5: Cross Site Request Forgery (CRSF) A6: Security Misconfiguration A8: Failure to Restrict URL Access A10: Unvalidated Redirects and Forwards A7: Insecure Cryptographic
As the result, we can able to describe the general accepted practice to determine the coefficient of permeability of silts and clay, identify the relationship between permeability
In addition, the Systems Support Group provide a system support helpdesk service, desktop support to users in Central Administration Departments, and are responsible for
Taking the enterprise group control theory and strategic cost management as a breakthrough point, this paper will study topics on how enterprise group could