Design and Analysis of Matrix Multiplication using IEEE 754 Floating Point Multiplier Partition Technique
Full text
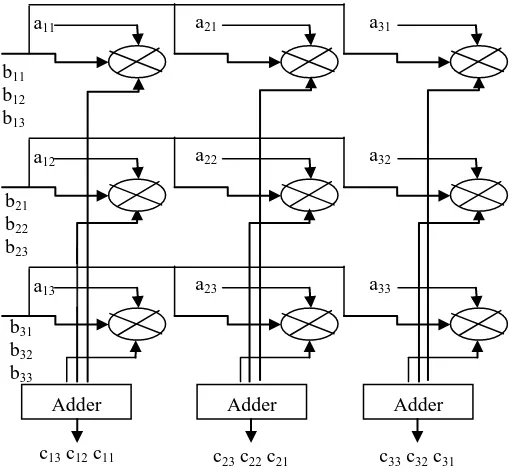
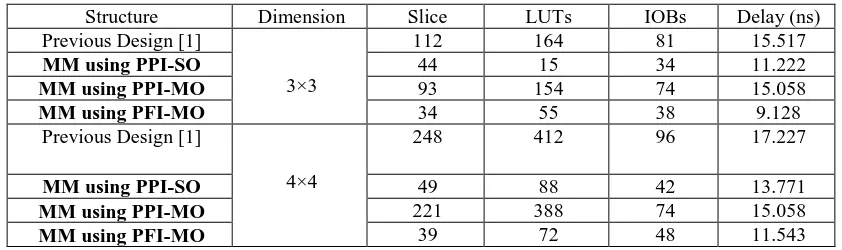
Figure


Related documents
[r]
To ensure the synchronization and encryption of data between the transmitter and the receiver, a feedback masking hyperchaotic synchronization technique based on a dynamic
Examining RQ1 ( What information do develop- ers need while using static analysis tools to diagnose potential security vulnerabilities? ) first, we identified developers’
Thus, the length of detected tracts reflects the gene conversion initiation rate rather than the real tract length, and GENECONV has very limited power when gene conversion is
Given a model where the probability of message losses is taken into account, the natural question to ask of a protocol is \Is the probability of something bad happening, in spite of
Two areas were investigated outside the limits of the ancient Agora. Since it is located only about 75 meters from the southeast corner of the Agora and the church lot
with commentary.. the letters of the word AE[X4o]t' were also lost. There is no evidence otherwise that the stone was broken at the right. I assume, therefore, that the only