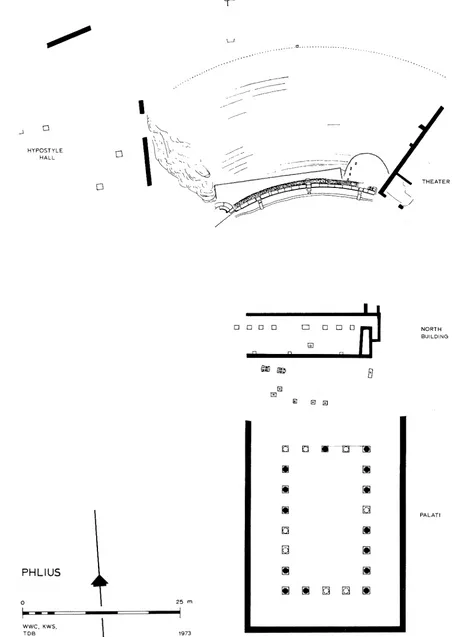
The Theater at Phlius: Excavations 1973
Full text
Figure

Related documents
The encryption operation for PBES2 consists of the following steps, which encrypt a message M under a password P to produce a ciphertext C, applying a
– ntop users can also monitor VoIP without having to use any specialized VoIP traffic analysis application (VoIP is not a first class citizen)?. – The use of
In summary, we have presented an infant with jaundice complicating plorie stenosis. The jaundice reflected a marked increase in indirect- reacting bilirubin in the serum. However,
In this study it is aimed to investigate the total lipid and the fatty acid composition of pearl mullet which is the only fish species occurring in Lake Van and
Fadugba will seek intervention of IATA in issues including: the harmful impact of the EU blacklist on the global reputation of the African airline industry; unilateral
This model satisfies the properties of conservation of the Boltzmann equation, and has been defined so as to allow for correct transport coefficients.. This has been illustrated
• how they and others choose and adapt features and functions of spoken language for specific purposes in different contexts. • some common influences on spoken language and