How the news media have failed to interrogate the concept of failed state, the case of Pakistan
Full text
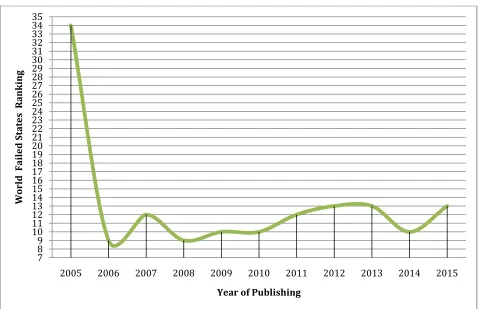
Figure



Related documents
messages for a project (as low as 0% and as high as 50% for a few projects), are missing data for our analysis. We considered several alternative strategies for handling this
This section is intended to provide a brief overview of DNS security issues, sections 5 and 7 look into more detail at two specific DNS security issues: cache poisoning
In addition, we compare two different receiving alternatives ± a reception box in the household and attended reception ± by simulating delivery times and home delivery efficiency.. As
The purpose of this study was to evaluate the rela- tive performance of 26 public urban transportation organizations in India using various criteria.. We grouped these 19 criteria
When studying the effect of water on nonwoven fiber PLA/NR during 180 days, it was determined that after hydrolytic degradation on the melting thermograms, the melting temperature (T
Commercial aircraft programs inventory included the following amounts related to the 747 program: $448 of deferred production costs at December 31, 2011, net of previously
Similarly, Jarvenpaa and Staples (2000) found that recognition and self-efficacy result in a culture of sharing. In the hacker communities, the handles become a pseudo-identity