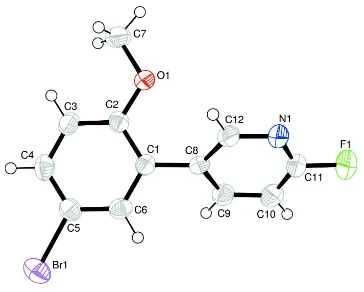
5 (5 Bromo 2 methoxyphenyl) 2 fluoropyridine
Full text
Figure
Related documents
Parr and Shanks [18] classify ERP implementations to three broad categories (comprehensive, middle road, and vanilla) and according to them ERP implementations differ with respect
There are different Session Key Exchange methods / algorithms Like Diffie-Hellman, Secure Hill Cipher Modifications and Key Exchange Protocol, Integration of
• Storage node - node that runs Account, Container, and Object services • ring - a set of mappings of OpenStack Object Storage data to physical devices To increase reliability, you
The algorithm will only match applicants employers preferred for NESP positions to NESP positions and applicants employers preferred for NETP positions to NETP positions. This way
Name And Brief Overview Of Contract Target Customer Groups Geographical Area Contract Start Date Contract End Date Key Performance Targets Actual Performance Local
In the previous sections, we dis- cuss the expectation that a neural network exploiting the fractional convolution should perform slightly worse than a pure binary (1-bit weights
Some properties are equipped with sophisticated electronics and stereo
• Our goal is to make Pittsburgh Public Schools First Choice by offering a portfolio of quality school options that promote high student achievement in the most equitable and