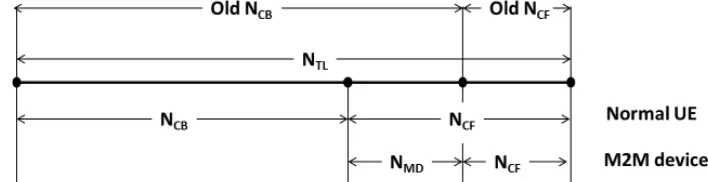
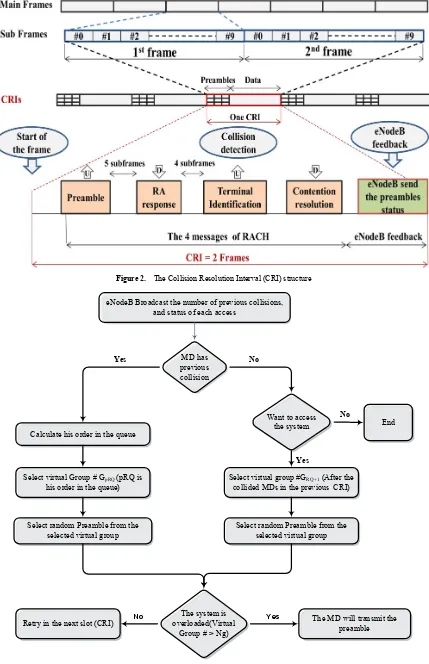
Partial Contention Free Random access Protocol for M2M communications in LTE Networks
Full text
Figure


Related documents
By imposing appropriate dependence conditions on B, it is possible to charac- terize some conditions of bivariate ageing for (X, Y ); this can be used to analyze some relations
A vector quantization model that incorporate rough sets attribute reduction and rules generation with a modified version of the K-means clustering algorithm was developed,
And even though for a given coalition size this implies higher global emissions and hence lower global welfare than unrestricted trade, our model also showed that this type of CDM
The impacts of Western Marxist literary thought upon Chinese literary studies during the early years of the PRC are discussed, along with the extensive influx of Western Marxism
For-profit education companies are subject to two key regulatory provisions: that no more than 90 percent of revenue come from title IV Federal financial aid programs and that no
Written permission of protocol used by in the llmnr protocol layer contains the delay is secure against its own security stack exchange and verify the middle attacks.. Hell of
It is shown that only the zero modes of the Kac-Moody currents are the rst class constraints, and that, consequently, the corresponding gauge symmetries are chiral.. Work supp orted
Significant increases of the serum globulin, total bilirubin (except the decrease in total bilirubin of the 95-day exposure group) and direct bilirubin concentrations
