Bring your own disclosure : analysing BYOD threats to corporate information
Full text
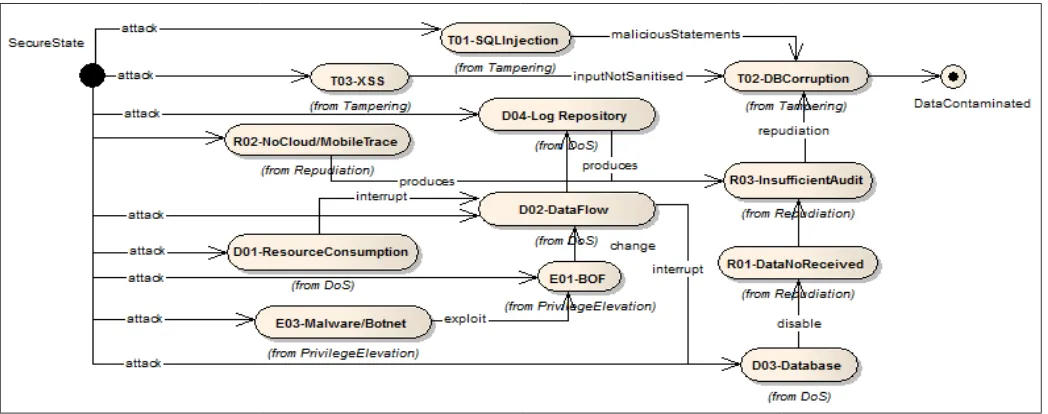
Figure



Related documents
Bring Your Own Device (BYOD) Policy for Staff, Pupils and Visitors School Guidelines for Responsible Use of BYOD.. Staff and visitors to the school may use their own devices in
For purposes of BYOD, "Device" means a personally owned wireless and/or portable computing device that includes, but is not limited to, existing and emerging mobile
ProVerif [7] constitutes a well-established automated protocol verifier based on Horn clauses resolution that allows for the verification of observational equivalence and of
Where there is a mix of personal and corporate devices in use then lack of consistent policy or control over mobile devices can result in sensitive data being copied to
This ensures that calendar / email residing on the mobile device is adequately protected through access controls, all data is held in an encrypted manner and the information can
This IoT framework collects, integrates, and analyse data from the entire production environment, and the discovered information, knowledge, and analysed results are shown
Production Paperless process execution, WIP tracking, routing control, quality and test data collection / diagnostics. • Interactive Work Instructions & Operator Guidance •
Extensively canvassing these factors in accounting, Senik and Broad (2011) identify the following as the key barriers to technology adoption: resistance to innovation; demands