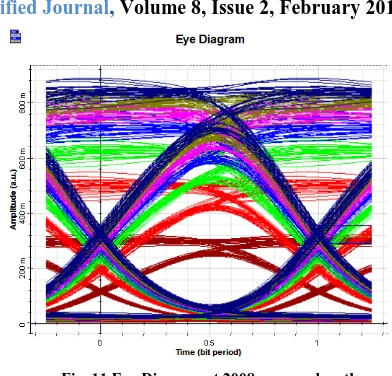
Performance Evaluation of DWDM Holmium Doped Fiber Amplifier for Optical Communication
Full text
Figure



Related documents
In Kaoru Kurosawa, editor, Advances in Cryptology - ASIACRYPT 2007, 13th International Conference on the Theory and Application of Cryptology and Information Security,
As a successful UK based managed hosting company which provides high quality Linux and Windows cloud web hosting solutions for small and medium sized businesses, Nimbus Hosting
Economic woes aside, proponents of this argument presented quotes from “experts” who argued that financial literacy programs were ineffective and amount to “little more than
Section II defines the specifications, additional to those for the basic td1 and td2 set forth in Volume 1 of Doc 9303, Part 3, to be used by States wishing to issue an
on deeply held misconceptions and fears of people who hold different beliefs, strategies of conceptual change theory, most often found in science education, were
The KKT condi- tions for NLP problems and the globally optimality properties of the convex programming (CoP) problems are usually applied to exploit these sufficient
drawers, a large breakfast island with a circular sink unit (H&C) with swan neck mixer tap, integrated Neff fridge, granite work surface area with base units to two
DISCUSSION: The Interim Utilities Director discussed the schedule of the project and special construction requirements. The Council questioned: the weather requirements, the