DATA LEAKAGE DETECTION USING ASP.NET AND PREVENTION
Full text
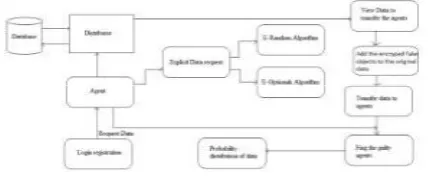
Figure
Related documents
The theoretical concerns that should be addressed so that the proposed inter-mated breeding program can be effectively used are as follows: (1) the minimum sam- ple size that
she has direct access to income and productive assets such as land , and not just access mediated through her husband or other male family members’P:30.. 1994:30) in cases of
Example: How to publish data in GDJ BADC Data Data BODC Data Data A Journal (Any online journal system) PDF PDF PDF PDF PDF Word processing software with
e , f The 18 F-fluorodeoxyglucosepositron emission tomography-computed tomography ( 18 F-FDG PET/CT) scan performed five months after starting cART showed intense accumulation
The first year program is mainly devoted to education, in the form of a series of seminars, and the development of the candidate’s individual research proposal.. In specific cases,
Building a new understanding of an information technology disaster recovery framework that focuses on traditional business interruptions and security responses that assist in
Strikingly, sIL-2R concentrations were significantly elevated in chronic liver diseases independ- ent of the underlying etiology, associated with the stage of liver cirrhosis
– Penetration price-a very low price designed to increase the quantity sold of a product by emphasizing the value.. Consumer