Surveillance and religion
Full text
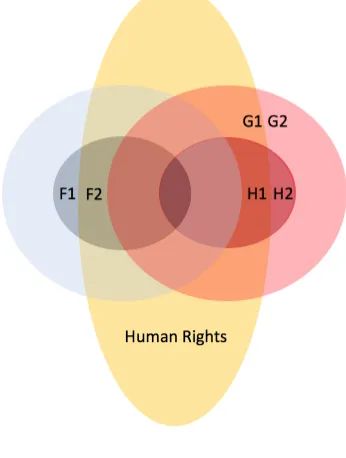
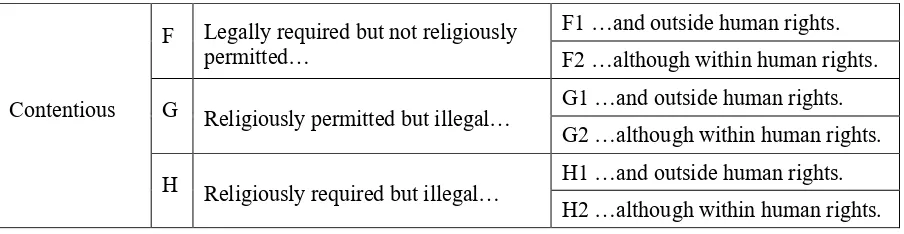
Figure

Related documents
There are obvious advantages to managing the risk in the supply chain
(Principal) School 7 Manufacturing and Engineering Alex (VET Coordinator) Tom (Principal) School 2 Aerospace Peter (HoD) School 8
ransomware shutdown Remote malware Drop Erase hard drives Erase hard drives malware Sleeper Ransomware Vandalism – delete files misoperation Remote shutdown Remote
Results of the survey are categorized into the following four areas: primary method used to conduct student evaluations, Internet collection of student evaluation data,
Peubah yang diamati dalam penelitian ini adalah kecernaan bahan kering (KcBK), kecernaan bahan organik (KcBO), dan kecernaan protein kasar (KcPK).Hasil penelitian ini
Keywords: Discrete cosine transform; Lossless coding; Data compression; Factorization of cosine matrix; Lifting matrix; Rounding-off; Integer DCT; Invertible integer DCT; Worst
Moreover, we show that the stability notions based on co- operative refinements do not conflict with efficiency in our class of payoff functions, however, the equilibrium selected
Configuring the Global Default Properties of the JMS Provider Service You can configure global properties of JMS virtual providers via the Config Tool1. Start the Config Tool