Standardized security assessment framework for ICS devices and pilot project
Full text
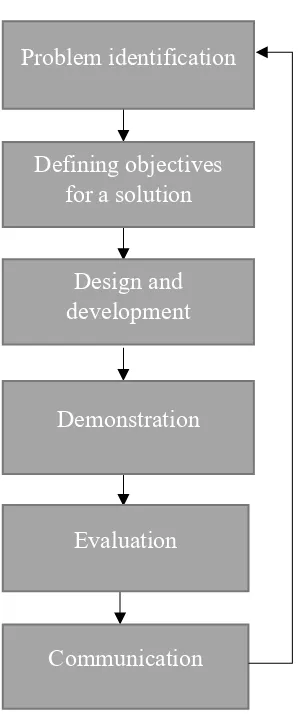
Figure



Related documents
To prevent offline access to mobile data on a server, the SAS Visual Analytics administrator assigns users or groups to a role that has the Purge Mobile Report Data capability..
Therefore, enterprises should consider one of the later communication protocols (such as 3G, Wi-Fi, etc.) for mobile devices used in business applications... MOBILE TECHNOLOGY
All mobile devices, whether owned by <Company X> or owned by employees, inclusive of smartphones and tablet computers, that have access to corporate networks, data and systems
Policy Name: IT and Mobil e Devices Security Policy Policy No: P04002 Approved Date: May 2014 Review Date: May 2016 Approved by: Senior Management Team EqIA Completed:
With these real-time quotes, the specialist on the Chicago Stock Exchange could guarantee to brokers that it would execute a retail market order to buy 500 shares of IBM at a price
Order ID PK Item Quantity Price Places Available Credit Sales ID PK Name Creates Item_ID PK Item Name Quantity Avaialble Checks Warehouse Worker ID PK Picks,Packs, Ships Removes
It may also be possible to shelter some or all of the gain from the deemed disposition or estate freeze using the $750,000 lifetime capital gains exemption for qualified
22 ABSCESS-DENTAL 23 ABSCESS- PERICEMENTAL 24 ABSORB 25 ACCELER GROWTH CONSCIOUSNESS 26 ACCELERATED PULSE 27 ACCELERATOR 28 ACCEPT 29 ACCEPTANCE 30 ACETABULAR LABRUM