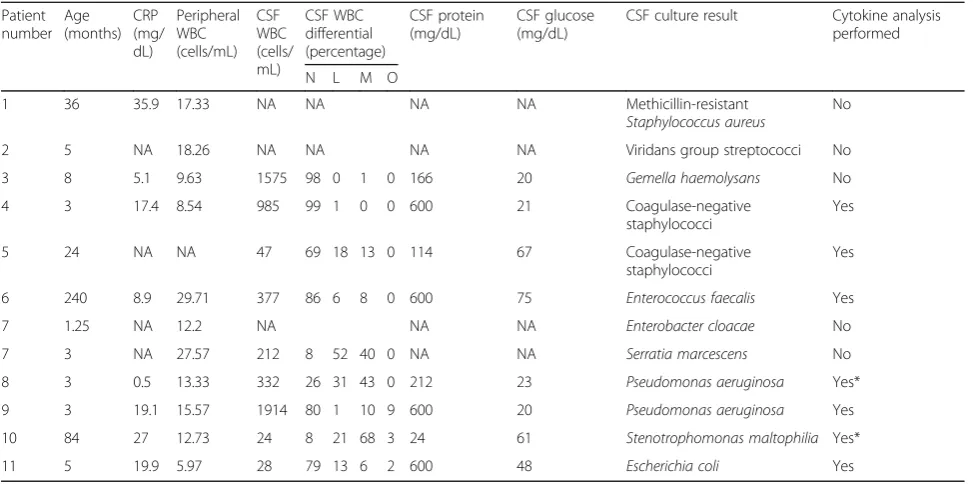
CSF inflammatory markers differ in gram-positive versus gram-negative shunt infections
Full text
Figure

Related documents
The probability of remaining in an internal state can be calculated using the sequential data, and the specific time period can be extracted as a stage of information processing
Our exploration goes further and, building on Askenäs (2000), proposes five roles that an information system may be allowed to take in an organisation: Bureaucrat,
zionamento Sociale: l’analisi dei dati di tre studi randomizzati controllati della durata di 6 settimane, per un totale di 1306 pa- zienti affetti da Schizofrenia acuta (Tab. V),
Captivity narratives are often regarded as the first genuinely American literary genre. From the origins in the British Barbary captivity narratives of the 16th
In contrast to rats receiving a normal diet or a 33% calorie-restricted diet, rats subjected to severe calorie restriction did not exhibit clinical signs of EAE.. Concomitantly with
To overcome this problem, an authentication system Pass Matrix, based on graphical passwords to resist shoulder surfing attacks is proposed.. With the help of one-time
Thus various Data mining techniques and web content mining tools are used to extract useful information or knowledge from web page contents. This paper focuses on web content
Clinical Psychiatry Research, Department Psychiatry, University of Sumatera Utara, Medan, Indonesia;. Bahagia Loebis , Prof,