Server Management Tool (SMT) 4.1
User’s Guide
(Linux Version)
Advanced Internet Technologies, Inc.
AIT Center
November 3, 2005
Revision History:This is version 4.1 of the SMT User’s Guide for Linux. All updates to this document will be noted below.
Version 4.1 • Updated Graphical User Interface.
• Revised functions for POP email and Email aliasing, including mail lists, virtual host email, and auto responders.
• Updated navigation from version 4.0 to include “Add” functions rather than “Provision” functions.
• Updated interfaces for FrontPage installation
• Updated interfaces for Virtual Host Control Panel (vpanel) installation.
• Updated interface for Anti-Spam Service, when ordered. • Updated for installation of Blog application.
Version 4.0 • Updated Graphical User Interface.
• Ability for I-MHIP plans to add and remove domains by the SMT functions.
• Integration of Billing Director into the SMT Interface. Preface:
This document is the user’s manual for the Server Management Tool 4.1 offered by AIT to all Linux web hosting customers.
Target Audience: AIT Customers
Table of Contents
To view a section, click on the link. This will take you directly to the area of your choice.
1.0 Introduction
2.0 Help
3.0 Bandwidth
3.1 Bandwidth for the previous day
3.2 Bandwidth by month
3.3 Bandwidth calendar
4.0 Server Info
4.1 Installed Perl Modules
4.2 Disk Utilization
4.3 Viewing Disk Usage by Day
5.0 Customer Care Center
6.0 Customer Console
6.1 Add (default view)
6.1.1 Virtual and Dedicated Servers 6.1.2 Create a Virtual Host Control Panel
6.2 Manage
7.0 Web Services
7.1 Add (default view)
7.1.1 Add Virtual Host
7.1.2 Enable Virtual Host Logs 7.1.3 Password Protected Directories 7.1.4 Add Web Stats Analyzer
7.1.5 Install Shopping Cart (MCart) 7.1.6 Install Webmail for Virtual Host 7.1.7 Install Bloggin for Virtual Host 7.1.8 Install cgi-bin for Virtual Host 7.1.9 Install Web Stats for Virtual Host 7.1.10 Install Chat for Virtual Host 7.1.11 Install mSQL
7.1.12 Install mySQL
7.1.13 Install Support Queue/CRM
7.1.14 Install FrontPage for a Virtual Host 7.1.15 Install File Manager for a Virtual Host 7.1.16 Install Guestbook
7.2 Manage
7.2.1 Manage Virtual Hosts 7.2.2 Add Mirror
7.2.3 Search for Virtual Host 7.2.4 Disable Virtual Host 7.2.5 Rename Virtual Host 7.2.6 Delete a Virtual Host
7.2.7 Change Your Main Server Password 7.2.8 Manage mSQL Server
7.2.9 Manage mySQL Server
7.2.10 Check Perl Scripts for Common Errors 7.2.11 Reset WWW Log Files
7.2.12 Untar a File
7.2.13 Set All CGI to Execute 7.2.14 Enable/Disable Telnet
8.0 Mail Services
8.1 Add (default view)
8.1.1 Add Email Accounts 8.1.2 Add Mail List
8.1.3 Add Email Addresses to a Mail List
8.1.4 Display List of Email Addresses in a Mail List 8.1.5 Remove Email Address to a Mail List
8.1.6 Setup Email Forwarding 8.1.7 Configure Email Responder
8.2 Manage (Mail Services)
8.2.1 Manage Email Accounts 8.2.1.1 Clear Mail 8.2.1.2 Modify User 8.2.1.3 Delete User 8.2.2 Manage Mail Lists 8.2.3 Delete Mail Lists
8.2.4 Manage Email Forwarding
8.2.4.1 Configure Default Mail Drop 8.2.4.2 View Aliases
8.2.5 Reset Anti-Relay Data File 8.2.6 Remove Auto Responders 8.2.7 Spam Prevention Tool
9.0 FTP Services
9.1 Add (default view)
9.1.1 Create FTP Account(s) 9.1.2 Setup Anonymous FTP
9.2 Manage
9.3 Manage FTP Accounts
9.4 Edit FTP Login Message
10.0 Additional Services 10.1 Order 10.2 Manage 10.2.1 Anti-Spam Service 10.2.2 Billing Director 10.2.3 Etools
10.2.4 Manage Payment Gateway 10.2.5 Premium Tech Support 10.2.6 Program Director 10.2.7 Utilize DB Manager 10.2.8 Web Stats Analyzer 10.2.9 Webmail
Introduction
The Introduction screen can be seen by users going in a web browser to http://theirdomain/cpanel/ or http://their.IP.address/cpanel/
The login for the SMT 4.1 is always ‘cpanel’ without the quotes, and the password is always the main server password. If this has not been changed by the user, then it is the same password that AIT provided the user after the setup of the account. Once logged in, the user will see the SMT Introduction screen, which should look something like what is displayed below in Figure 1-1.
Figure 1-1
If you are a first time user of the SMT 4.1, please review the instructions indicated in the middle of the screen.
Help
Throughout the SMT 4.1 interface, you will see the following icon (Figure 2-1). This icon is a short help section and is displayed on almost all of the interfaces a user will use in the SMT 4.1.
Figure 2-1
Also, the “Help” link at the top of the screen provides the user with simple links to areas that provide additional help. These areas include AIT101 for Beginners, Frequently Asked Questions (FAQ’s), and other support systems. Figure 2-2 below shows an example of this screen.
As an added benefit of this User’s Guide, we have added in sections named “Why would I need to know this?” which are placed in specific areas in the User’s Guide to show the value of particular features.
Bandwidth
The “Bandwidth” link is located under “Home” in the navigation menu, and is also located on the top of the screen. Once the page loads, the user will see something like what is in Figure 3-1 below. This interface shows the data transfer that the user’s account has used during a specific period of time. This graphically displays the amount of data transferred for HTTP, SMTP, POP and FTP services, as well as other Internet services that are less common. Also, this interface displays the raw data that can be viewed in several different formats.
Figure 3-1
Bandwidth for the previous day
On the upper right hand corner of the interface, the user will see the data
transferred, by service, for the past 24 hours. Figure 3-2 below shows an example.
Figure 3-2
Bandwidth by month
Figure 3-3 below shows the total data transferred for the month. The bandwidth total is listed on the far right hand side, and each service common to web hosting is listed to the left of the total.
Figure 3-3
Bandwidth calendar
On the upper left hand side, a user will notice a calendar. If the user selects a date by clicking on a day of the month, the right hand side of the interface will update with the data transfer information for the date selected. The user can select the year and month options as well by clicking the drop down menus or by clicking the arrow buttons to the left and right of the month/date drop down menus. Figure 3-4 below shows an example of the calendar and how it displays.
Figure 3-4
Why would I need to know this? This information is good for analyzing site traffic, and overall bandwidth usage. This tool will prevent your account with AIT from going over its allotted data transfer limit without you knowing ahead of time.
Server Info
The “Server Info” link, located on the top of the screen or under “Home” in the sidebar navigation, can be used to determine the operating system, and the versions of software and applications installed on the user’s account. Also, this area has separate links to show the installed Perl modules, and the Detailed Disk Utilization. Figure 4-1 below shows the default screen for Server Info.
Figure 4-1
Installed Perl Modules
Figure 4-2 below shows the results of clicking the “Click to View” link beside the Installed Perl Modules. This list shows the Perl modules, by name, which are
installed on the server. If the user does not see modules that need to be installed on the account, the user should download or obtain a copy of the module, and put it on
the server in a directory in the root of the server. Then, proceed to the Online Customer Care Center and order the Perl Module installation.
Why would I need to know this? AIT charges to install additional Perl modules, so before requesting extra modules and paying to have the installed, the user should know what Perl modules come with the account by default.
Disk Utilization
Also, the bar at the bottom of the “Server Info” page is a link for “Click to View” for disk utilization. This provides the user with a breakdown, directory by directory on the server, of how much disk usage is being used and in what directory. When run, the report will look something like Figure 4-3 below.
Figure 4-3
Why would I need to know this? Much like the Traffic Monitor that is listed in the beginning of the User’s Guide, this tool shows users what their disk utilization is at any time, along with a history (see below) of disk usage for the past 30 to 60 days. This will ensure the user stays within the allotment that comes with their AIT hosting package.
Viewing Disk Usage by Day
When on the screen displayed in Figure 4-3 above, a user will notice two links at the top of the page. These links are for the current month disk usage by day, and for the previous month’s disk usage by day. When these links are clicked, they will display something like what is displayed in Figure 4-4 below. This is the total in MB per day. Each day is listed on a separate line; disk usage for each day is to the left of the date.
Customer Care Center
The AIT Online Customer Care center is used to order new products and services. To login, use your customer number and your billing password. If a user has forgotten their password, they can click the link below the login section (See Figure 5-1 below) and provide their customer number. The password will be emailed to the account owner. If a user has forgotten their Customer number, the AIT Sales team can provide it after verifying that the person claiming to be the account owner really is. In addition, the Care Center allows users to view their most recent invoices and statements. For the best view of all transactions, use the “View Statement” option available after login.
Customer Console
The “Customer Console” link on the left navigation will display the “Add” section by default. In this section, a user can add Virtual and Dedicated Server SMT interfaces inside the SMT interface that the user is logged into, or a user can create a Virtual Host Control Panel for a domain name hosted on the user’s account.
Virtual and Dedicated Servers
In this section, a user can add additional domains that are not virtual hosts, into the management interface of the SMT 4.1. For example, if a user has another account hosted with AIT (another Dedicated server, for instance), adding the domain name in the filed provided will provide a fast and easy link from the SMT that the user is currently in to the SMT of the Dedicated server.
Create a Virtual Host Control Panel
To create a Virtual Host Control panel, otherwise referred to as a “vpanel,” click the “Display list” button under the directory name (See Figure 6-1 below). This will display a list of directory names inside of the user’s /www/htdocs directory, along with a list of domain names hosted on that account. Enter the password and confirm it before clicking the “Create vpanel” button to install the vpanel.
Figure 6-1
IMPORTANT NOTE: The username of the vpanel is the “webadmin@domain” where the domain name is the domain you installed the vpanel for. For example, if a user installs a vpanel for a domain name called “test.com”, this is how the user would access the vpanel for test.com:
URL: http://test.com/vpanel/ Username: [email protected]
Password: <password input on the web form in Figure 6-1>
This is different than in previous versions of the SMT, so please take note of the change.
Manage (Customer Console)
The section labeled “Manage” under Customer Console allows users to click links directly to the SMT interfaces of other domains (see Virtual and Dedicated Servers or Create a Virtual Host Control Panel for how to add them into the interface). The links inside of this section directly link to the Customer Console for either a virtual host (vpanel) or another Virtual or Dedicated server (SMT) as Figure 6-2 below shows. Not shown in Figure 6-2 are the links for other Virtual and Dedicated Servers.
Web Services
The default view when selecting Web Services is the “Add” view. Under this section, users can manage services used to view web sites, including addition and
management of domain names, mirror domains, logs, password protected directories, etc.
Figure 7-1 below shows the default screen when clicking on “Web Services”.
Figure 7-1
Add a Virtual Host
To add a virtual host domain name to the account, while at the screen displayed in Figure 7-1 above, click the “Add Virtual Host” link. Figure 7-2 (see below) will then be displayed. To complete the form, the user must enter the following information:
• Fully qualified domain name (ex. domain.com). Ensure the user does not include ‘www’ in front of the domain name.
• Home directory (not path) for the files for the virtual host domain name (ex. domaincom or domain). This directory will be located in the /www/htdocs directory by default. This directory can be viewed by telnet or FTP.
Figure 7-2
After the domain name has been added, the user will see the screen below (Figure 7-3) that displays the success message, along with the links to the Virtual Host
Figure 7-3
NOTE: Please be aware that if you have a legacy account (i.e. Server 2, Server 2 Plus, etc), the feature to add a domain will be disabled, and you can only add a domain name through the Customer Care Center link.
Enable Virtual Host Logs
From the “Add” menu under Web Services, a user can add web logs to a domain that is hosted on that account.
To enable or disable both Error and Access (traffic) logs for a specific domain, select the domain name from the drop down menu and then click the appropriate radio button for either the Error or Access log. Note that if the user selects “Enable”, visits to the website from that point forward will accumulate in the logs. Each virtual host log file is located in the /www/logs directory of the server by default, and can be found in FTP or telnet at that path. Figure 7-4 below shows an example of what the SMT would look like prior to the enabling of logs for a domain name called
Figure 7-4
Why would I need to know this? Web logs validate traffic to a website, and provide information about visitors, including but not limited to the date and time they visited the web site, the files and directories they visited, the operating system and browser type of the visitor, the web site they can from, and many other
features. For AIT Resellers, this is a valuable feature to sell your customers because it means their logs can be analyzed by the most commonly used programs available, like Webalizer, Analog, Urchin, and Web Trends. AIT only supports Webalizer on its hosting platform; however, logs can be downloaded and analyzed by any application. Once enabled, there will be a result at the bottom of the screen stating success or failure (Figure 7-5). Please note that Access logs are also sometimes called Transfer logs.
Figure 7-5
Password Protect a Directory
There are 3 key steps to password protecting a directory; they’re listed in order in the SMT 4.1. Step 1 is to make sure that the Apache or Web server settings are correct. To verify the settings for your account, click the link under Step 1 (See Figure 7-6).
Figure 7-6
Once the link has been clicked, you will either receive a success message or a failure message (Figure 7-7 below). Usually a failure is not a problem, as your account can be setup to accept the changes that we are about to make. The configuration change that this first step provides is the ability to create an “.htaccess” file in any directory that you wish and have the Web server (Apache) understand that this “.htaccess” file is the authority for password protection.
Figure 7-7
If the message is failure but it states that “.htaccess files are already allowed on your server”, then you can proceed to Step 2. If not, contact AIT Customer Service for a review of your Apache configurations.
In step 2, input the following required fields (Figure 7-8 below):
• Path – This should be the full path (not URL) to the directory that requires password protection. Reviewing the full path in an FTP program or via Telnet is advised here. (ex. /www/htdocs/protected)
• User Name – This is the first username you will give access to this password protected area. You can add other usernames later; however, there is a requirement that one user must have access when creating a password protected directory. (ex. testuser)
• Description Heading – This section is just a simple phrase that will be included in the username/password field when someone is prompted to input a username and password. In this case, we used “PPD Test”.
Figure 7-8
Upon submission of the form available in Step 2, you may receive a success or error message. A somewhat common message that will appear after the submission of this step is the error displayed in Figure 7-9 below. If a directory has been
configured for MS FrontPage, then the .htaccess file will require manual editing. For this, please consult (carefully) documentation on the Internet regarding .htaccess files and FrontPage configurations, or contact AIT’s Customer Service Department and we can assist with the editing of these files.
Figure 7-9
If the user does not receive an error, they most likely will receive the message in Figure 7-10, which shows the contents of the .htaccess file and a success message for the creation of the .htaccess file in the proper directory.
Figure 7-10
Step 3 of the process requires the addition of the username and password to a file back in the directory structure called an “htpasswd” file. This file contains the encrypted passwords for the users who have access to the password-protected directory. To add users to the htpasswd file, complete the form for Step 3 (Figure 7-11). Included in this form are the required fields, which are:
• Path to htpasswd file – The default of /usr/local/etc/htpasswd is a good place to store your file as this is not web accessible.
• Username – The username can be between 3 and 8 characters long.
• Password – As in any web service, the password MUST be between 6 and 8 characters, and SHOULD contain letters and numbers. For security reasons, it should not be set to anything simple such as love, password, or 123456.
Figure 7-11
Why would I need to know this? From time to time, some of a user’s customers may want to have a members’ or protected area. This allows AIT account holders to quickly setup password protected areas of a website, limiting access to specific users. Please note that this is NOT providing someone with FTP access only to their directory. This is for web browsing only, not for FTP services.
Add Web Stats Analyzer
Instructions on this section can be found in the Install Web Stats for Virtual Host section. The only difference is that the form will automatically fill in the top level domain name.
Install Shopping Cart (MCart)
* Please see the User’s Guide for MCart located at
http://support.aitcom.net. If you are unfamiliar with this product, please review the User’s Guide first.
This will you install Mcart, AIT’s customizable shopping cart. This function will install Mcart for the main account, as well as all virtual hosts. Figure 7-12 below shows the installation form. The steps below outline what should appear in the form.
• Mcart Version to install/upgrade – The user must select the option that best describes how the payment process will be handled.
• Directory to install/upgrade shop in – The user will specify the directory path for the MCart. The MCart should be installed in a directory within /www/htdocs. If the MCart is to be installed for a virtual host, the path should be specified as being for a virtual host. AIT recommends that you use /www/htdocs/vhdir where vhdir is the directory name for the virtual host domain name.
• Username for Shop Administrator –This field can remain as
‘shopkeeper’, unless the user wants to specify a preferred username for access to the administrative section of the MCart.
• Password for Shop Administrator –The user will enter the preferred password for access to the administrative section of the MCart. As in any web service, the password MUST be between 6 and 8 characters, and SHOULD contain letters and numbers. For security reasons, please avoid passwords such as love, password, or 123456.
• Re-enter Password – The user will need to re-enter the password to confirm that it is correct.
Select ‘Setup Shop’ and the MCart will be installed in the specified directory.
Figure 7-12
Install Webmail for Virtual Host
This feature enables the user to access email from a web browser. To use this function, the POP email account must currently exist on the server. See Add Email
Accounts to add the account if it does not exist. To install this feature, complete the form displayed in Figure 7-13 below:
• Domain Name – This is the domain name that will send email. ex. vhdir.com if the email address is [email protected]
• Directory - The directory location to install the webmail application. The directory name that is input will be the name of the directory created after the document root of the domain. For instance, if the domain name is ‘domain.com’ and domain.com is a virtual host pointed to the directory ‘/www/htdocs/domaincom’, then the ‘webmail’ directory will be created after ‘domaincom’. The name to give the directory is not a path, just a directory name.
Figure 7-13
Once webmail is installed successfully, the user can login to the webmail application to make additional changes to the look and feel. Figure 7-14 below shows the interface after the installation is successful and the administrator login has been used.
Figure 7-14
Install Bloggin for Virtual Host
The Blog application that is in the SMT 4.1 can be installed on your top level domain, or any virtual host. To install the blogging application, simple select the domain name that you wish to add the blog to, and then add a directory name. Figure 7-15 below shows an example of what can be used.
• Domain Name – This is the domain name that will have the blog installed.
• Directory - The directory location to install the blog application. The directory name that is input will be the name of the directory created after the document root of the domain. For instance, if the domain name is ‘domain.com’ and domain.com is a virtual host pointed to the directory ‘/www/htdocs/domaincom’, then the ‘blog’ directory will be created after ‘domaincom’. The name to give the directory is not a path, just a directory name.
Figure 7-15
After the blog software is installed, it can be configured by the Blog administrator. Upon installation, an administrative username/password will be given to the user for use. Below in Figure 7-16 is an example of the default screen once the Blogging application is installed.
Figure 7-16
To finalize any configurations, you can edit the files of the blog via your favorite web editor, or you can customize the interface by logging in as the Blog administrator using the ‘Set Colors’ feature.
Install cgi-bin for Virtual Host
This feature installs the cgi-bin, or a directory where CGI and Perl scripts can be executed from for a virtual host. The cgi-bin will be installed in the document root for the virtual host. (ex. /www/htdocs/vhdir/cgi-bin where the virtual hosts document root is /www/htdocs/vhdir). To install the cgi-bin, complete the form field as displayed in Figure 7-17 below:
• Virtual Host Domain – Domain name of the virtual host for whom the cgi-bin is being installed.
Figure 7-17
Successful installation of the cgi-bin will produce the ‘Success’ message. Any errors should be reported to the Customer Service/Technical Support Department.
Install Web Stats for Virtual Host
This option installs the Webalizer software for virtual host accounts. This software provides the user with statistics such as the number of hits and views a website has generated, and referring URL’s. Before a virtual host can have or utilize Webalizer, logs must be enabled for the virtual host domain name. To enable logs, please review the Enable Virtual Host Logs section of this User’s Guide.
Once the logs are installed, the user can install Webalizer. To install the software, complete the form as illustrated in Figure 7-18. All of the form fields under Top Table Keywords have explanations; therefore, none are included here.
• Domain Name – The user will input or select, from the list, the virtual host domain name for which Webalizer will gather statistical data. This field will be left blank if the user is installing Webalizer for the main account.
• User Name – The username to enter to access Webalizer for the specified domain. Access to this data requires authentication.
• Password – The password to enter to access Webalizer for the specified domain. As in any web service, the password MUST be between 6 and 8 characters, and SHOULD contain letters and numbers. For security reasons, do no use passwords such as love, password, 123456.
• Verify Password – Re-enter the password to confirm it was entered correctly.
Figure 7-18
Once installed, Webalizer must be checked at least every 30 days. If this is not done, then data (logs) could be missing from the Webalizer interface.
1. Administrative user must login to the appropriate URL for Webalizer for the domain name (traditionally its domain.com/webalizer/)
2. Administrative user must click the “Run stats” button so that logs are read into the Webalizer configuration files.
3. Administrative user can then click the “View Stats” button to review the most up-to-date stats for the account.
4. The Administrative user can then reset the log files for this virtual host domain by removing them from the /www/logs directory on the server to conserve disk space.
This feature will install the files necessary to run Chat on the account. The user must first install the chat server before installing the client. To use this feature, complete the form fields displayed in the screen shown in Figure 7-19 below. First, select the button labeled “Install Chat Server”. This will install the files necessary to run the chat server.
Figure 7-19
Next, complete the form fields under “Chat Client Installation” section.
• Installation Directory - The user will specify the directory path for the chat client. The client should be installed in a directory within /www/htdocs. If the chat client is to be installed for a virtual host, the path should be specified as that of the virtual hosts. It is recommended to use /www/htdocs/vhdir where vhdir is the directory name for the virtual host domain name.
• Virtual Domain - Domain name of the virtual host for which the user wishes to install the chat client.
Upon installation, the user can begin chatting by going to the directory specified in the form field that was completed at the time of installation.
Install mSQL
This feature is used to install the mSQL software on the server. MSQL (or mini SQL) is database management software that provides fast access to stored information. Once the option has been selected, the software will be installed at
/usr/local/msql2.0/ at the root of the user’s server.
Install mySQL
MySQL is a relational database management system, which means it stores data in separate tables rather than putting all the data in one big area. This adds flexibility, as well as speed. The SQL part of MySQL stands for "Structured Query Language,"
which is the most common language used to access databases. The MySQL database server is the most popular open source database in the world. It is extremely fast and easy to customize, due to its architecture. Extensive reuse of code within the software, along with a minimalist approach to producing features with lots of functionality, gives MySQL unmatched speed, compactness, stability, and ease of deployment. Their unique separation of the core server from the storage engine makes it possible to run with very strict control, or with ultra fast disk access, whichever is more appropriate for the situation. Once the installation option is selected, MySQL is installed to the /usr/local/mysql directory.
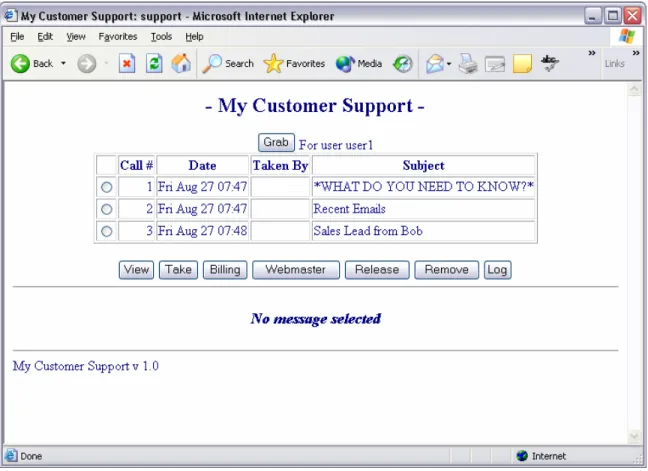
Install Support Queue/CRM
This feature enables the user/reseller to create an email-based support system to assist customers with issues. It is normally used for customer service functions like billing, technical, or website related issue, but the user can deploy it for other reasons if need be. The installation of this software will enable the user to post a support page for their customers. All support requests will be sent to the email addresses specified in the form fields. The user may add up to four guest accounts for the support queue application.
To install the software, complete the form as illustrated in Figure 7-20 below.
• Support System Name – This is the name that will appear at the top of the support page
• Email Alias - The email address that the user wants support messages delivered to.
• Billing Issue Email: The email address the user specifies for receiving billing inquiries.
• Webmaster Issue Email: The email address the user specifies for receiving webmaster inquiries.
For Each Username added to the CRM/Support Queue, up to 5 users, the user will add the following:
• User Name - The username to enter to access the administrative section of the support queue.
• Password - The password to enter to access the administrative section of the support queue.
• Email Address: The email address the user specifies as the address to which all emails are delivered.
Figure 7-20
Once installed, any of the servers used to create the Virtual Support Queue will login to it. They will see something like what is displayed in Figure 7-21 below.
Figure 7-21 Button functionality after call is selected:
• View – Views a call at the bottom of the screen. Does not send the user email.
• Take – Sends the user email and marks the call as taken by that user.
• Billing – Sends the call to the billing email address and removes the call from the Queue.
• Webmaster - Sends the call to the webmaster address and removes the call from the Queue.
• Release – Removes a user’s hold on a call. This can only be done by the user who owns the call.
• Remove – Removes the call from the Queue.
• Log – Shows the log of the last 200 or so calls that were removed from the queue and by what user.
• Grab – Does both the “Take” and “Remove” function at the same time.
Install FrontPage for a Virtual Host
This feature is used to install the Microsoft FrontPage extensions for virtual hosts. While the MS FrontPage software is not supplied by AIT (it must be purchased by the client), AIT does install the FrontPage server side extensions, which are required to utilize many of the features of MS FrontPage.
• Enter a Virtual Host – The user will select from the list the virtual host domain name for which FrontPage should be installed.
• Enter User Name – The username to enter in FrontPage to access the specified domain.
• Enter Password – The password to enter in FrontPage to access the
specified domain. As in any web service, the password MUST be between 6 and 8 characters, and SHOULD contain letters and numbers. For security reasons, do not use passwords such as love, password, or 123456.
Figure 7-22
Once the user has completed all fields in the form, the form must be submitted. The figure below displays the results when MS FrontPage extensions have been installed successfully.
Figure 7-23
Install File Manager for a Virtual Host
This feature enables the user to install an application that will manage the amount of data that a client can install to a specified directory. The user will be able to utilize a web interface to upload, download, modify, and delete files. The file manager will be installed in the directory specified by the user and will only work for the specified directory. The user may install the file manager for multiple directories.
To install the software, complete the form as illustrated in Figure 7-24.
• User Name – The username to access the file manager for the specified domain.
• Password – The password to access the file manager for the specified domain. As in any web service, the password MUST be between 6 and 8 characters, and SHOULD contain letters and numbers. For security reasons, do not use passwords such as love, password, or 123456.
• Verify Password – Re-enter the password to confirm it was entered correctly.
• Domain Name - The user will enter the virtual host domain name for which the file manager is being installed.
• Disk Usage Quota – Input the maximum number of data in megabytes (MB) allowed to be installed to this directory. The user needs to ensure this
• Installation Directory - The user will specify the directory path for the installation of the file manager. AIT recommends using /www/htdocs/vhdir where vhdir is the directory name for the virtual host domain name when installing this application for virtual hosts.
Figure 7-24
Once the user has completed all fields in the form, submit the form. Upon submission, the user can log into the File Manager.
Install Guestbook
This section creates a web-based Guestbook using a popular script. The installation is a simple form with the form fields listed below and shown in Figure 7-25.
• Domain Name – This field specifies the domain name for the Guestbook. The option to display the domain name for all domains on the server is also listed.
• Receive Email from Guestbook – If this is set to “Yes”, then the site administrator email address below will receive emails when postings are submitted to the Guestbook.
• Email Address – This is the email address used for the Guestbook additions. If the above entry is set to “No”, then this email address field can be left empty.
Figure 7-25
Upon completion, Figure 7-26 below shows what the guestbook pages will look like by default. These pages can be changed; however, please be careful not to remove any specific code used by the application.
Manage (Web Services)
Under the Manage Web Services options is a group of good management tools for web site owners. In this section, you will see a quick link menu (Figure 7-27 below shows the screen with some commonly used features).
Manage Virtual Hosts
The “Manage Virtual Hosts” option is the area where users can add, delete, rename and disable additional domains (virtual hosts) on an account. The top menu will allow the addition of Virtual Hosts and Mirrors, as well as the Search feature that is useful for accounts with more than 15 domains. The default display on this page (Figure 7-28 below) is 15 domains at a time, listed alphabetically.
Add Mirror
A Mirror or Mirror Domain is a domain name that “mirrors” another site currently hosted. This is treated as a virtual host, and counts towards the quota of additional domains allowed on your account.
Why would I need to know this? The ability to add and remove Mirror domains is best used for search engine placement. An example of this would be
mydomain.com, and mydomain.net. If the user already has the domain
mydomain.com as an existing website, the domain mydomain.net can be added as a mirror of the site mydomain.com. To create a Mirror, the user will always need the existing site, and the new domain that should mirror the existing site.
To add the mirror, enter the new domain name in the “Domain Name” section and then select the pre-existing domain name to mirror the new domain to. Figure 7-29 below shows an example of what the user will see.
Figure 7-29
Search for Virtual Host
The Search feature will allow users to quickly find domain names on the account. Domains may be found by simply entering the domain name in the search box (Figure 7-30). The search is sensitive, so if you search for ‘domain’ when looking for ‘domain.com’, the search will find it. The results (Figure 7-31) will still allow for the basic features of deactivation, renaming and deleting.
Figure 7-30
Disable Virtual Host
The ability to disable a virtual host is done directly from the “Manage Virtual Hosts” area. Simple clicking the link will update the web server configuration files, and the site will become disabled. Figure 7-32 below shows an example of the site
‘testing14.com’ being disabled. Note that only Web Services (HTTP) are disabled; FTP, SMTP and POP services are not. It is recommended that any FTP user account be removed during a disabled action.
Figure 7-32
Why would I need to know this? The ability to disable a domain is very
for services rendered. This disable feature allows web services resellers to suspend accounts until payment is received.
Rename Virtual Host
The screen below shows how a user can rename a domain name. The purpose behind this feature is to change the domain name that is pointed to a directory on the user’s virtual server. Once the “Rename” link is clicked on the list of all virtual host domains, the screen below (Figure 7-33) will appear. Please note that this feature does not register or renew a domain name. It will only rename the domain configuration on the virtual server for HTTP, FTP, SMTP and POP traffic.
Figure 7-33 Delete a Virtual Host
From the main list of domains, there is an option to “Delete” a virtual host domain. When clicking the link to “Delete” for a specific domain, you will receive a pop up display asking if you wish to delete the domain (Figure 7-34). Once a user selects “Yes”, the domain will be deleted from the user’s virtual server. This will remove all configurations for that domain name; however, it will NOT remove the data inside of the directory or document root for the domain. This is something that will need to be done by hand using FTP, telnet or another scripting method. Once a domain is deleted, the quota for allowed domains on the virtual server will increase by one.
Figure 7-34 Change Your Main Server Password
Changing the main server password is a very simple procedure; however for security reasons we always recommend that users change their password every 30 to 60 days. The user should ensure the password is between 6 and 8 characters, and should include both letters (upper and lower case) and numbers.
This password is used for both SMT/cpanel access, as well as FTP access. Figure 7-35 shows an example of a cryptic password.
Figure 7-35
Manage mSQL Server
This section is used to manage mSQL. mSQL or “Mini” SQL, is a database application used by web developers to make websites with dynamic content. The features shown below in Figure 7-36 are the only management functions needed in the
SMT/cpanel. This provides the ability to start, stop and restart the mSQL “daemon” or service. Please note that this is not a utility for MySQL.
Figure 7-36
To start the daemon or service, simply click the “Start/Restart mSQL Server” link. The output (See Figure 7-37) will show that the service started successfully.
Figure 7-37
Manage mySQL Server
This section is used to manage MySQL. MySQL, is a database application used by web developers to make websites with dynamic content. The features shown below in Figure 7-38 are the only management functions needed in the SMT/cpanel. This provides the ability to start, stop and restart the MySQL “daemon” or service. Please note that this is not a utility for mSQL.
Figure 7-38
To start the daemon or service, simply click the “Start/Restart MySQL Server” link. The output (See Figure 7-39) will show that the service started successfully.
Figure 7-39
Check Perl Scripts for Common Errors
This feature helps check perl scripts for simple errors. The error checking is done by a program in the SMT/cpanel. See Figure 7-40 for an example. This program will test 4 areas:
TEST 1: script and permissions
This test ensures that the file exists in the location specified on the virtual server, and that the permissions and ownership are properly set. For example, if the perl script that a user is checking is found to be 644, or not executable, it will correct the permissions and change the script to 755, which is executable permissions.
TEST 2: script file format
This test ensures that the file was uploaded in ASCII (pronounced “asky”) mode and not binary mode. It will strip out any unwanted characters that sometimes can’t be seen on a Windows operating system.
TEST 3: check perl path
This test checks the path at the top of the perl script and ensures that it is set to the location where the perl binary is located on the virtual server. The path to perl, or the first line in any perl script should always be one of the following two lines. #!/usr/bin/perl
#!/bin/perl
This test reviews the basic syntax of the perl script. It may find simple errors, and correct them or point them out; however, this is a cursory review of the syntax, and will not evaluate logic errors. Scripts that are found freely on the Internet should work out of the box with some simple configuration changes. This test should inform the user whether the syntax for those changes is correct.
If the script passes all the tests but still won’t run, it could be one of the following areas.
• Make sure it can find any files or external programs it needs • Make sure any included perl programs also check out
• Make sure you are writing a "Content-type:" line at the beginning of the script’s output
Figure 7-40
Reset WWW Log Files
This feature will reset or “zero out” all web server logs in the logs directory for the top level domain name. The files that are reset are as follows:
/www/logs/access_log /www/logs/error_log
NOTE: This feature does NOT reset log files for virtual host domains on the server.
Log files for each virtual host will need to be zero’ed out by FTP, telnet or other scripting means.
Figure 7-41
Untar a File
The ability to untar or decompress a file using the SMT/cpanel means that a user does not need to have or use telnet access. If a user wishes to put software or files that are in a tar format on the server, they can use this SMT feature to upload a small, compressed file, and expand the files on the server. This saves on upload time and also on data transfer.
To untar a file, complete all 3 input sections. See Figure 7-42 below as an example. • Path to the tar file – This is the complete directory path, from the root of
the virtual server to the file that has been uploaded via FTP.
• Path to untar the file in - The directory you are untarring to will need to exist. You can create this via FTP.
• Type of operation – Select Uncompress, Untar or Gunzip. These are the most commonly used compression algorithms. If a user is unsure of what operation to choose, the user can simply review the file extension of the compressed file and compare it to what is on the interface. The file extensions match the action to execute.
NOTE: Files in the /www/logs directory will not be untarred by this page. You will need to contact AIT to do so. Also, files will not be able to untarred to /bin, /usr/bin, /lib, or /usr/lib. This is because files in these directories are unavailable to users.
Figure 7-42
Set All CGI to Execute
This feature will set all programs in the /www/cgi-bin directory to 755, or executable. The file permissions of executable tell the browser or user if they can access and execute the file. CGI or perl programs need to be executable to be viewed. Typically, after uploading a CGI or perl script, a user will need to change mode or chmod the file to 755 permissions. The numerical value of the permissions can be understood by using the chart below. In FTP, or telnet, users can see the file permissions by doing a directory listing. Here is an example of what can be seen in FTP or telnet.
-rwxr-xr-x 1 523 523 8953 Jul 2 17:01 fmail.pl
Note the permissions column on the left hand side. The “r” means that the file is readable. The “w” means that the file is writable and the “x” means that the file is executable. These permissions are duplicated for 3 groups. They are the super user
first, the user, then the group permissions. Here is a visual sample. Green is the super user, blue is the user, and red is the group.
4 + 2 + 1 4 + 2 + 1 4 + 2 + 1 = 777
r w x
r w x
r w x
The chmod or change mode to the correct permissions can be done one file at a time via FTP or Telnet, or the tool in the SMT can be used to conduct this chmod to 755. In Figure 7-43 below, you can see that the user can do all this with the simple click of a button.
Figure 7-43
Enable/Disable Telnet
This feature allows you to enable and disable telnet access. Telnet is the Internet standard protocol for remote login (terminal connection) service. TELNET allows a user at one site to interact with a remote timesharing system at another site as if the user's terminal were connected directly to the remote computer. In Figure 7-44, you can see the simplicity in performing this task.
Mail Services
The “Mail Services” link on the left navigation will display the “Add” section by default. In this section, users can add, modify or delete email settings and
configurations. Figure 8-1 below shows the default view, and the links that will be displayed at this main “Mail Services” menu.
Figure 8-1
Add Email Accounts
This feature will allow users to add email boxes or POP accounts. This means that the user will have a mailbox on the server where email will be stored. User’s can use web based email, or use email clients such as Outlook or Outlook Express to
download the email they receive.
Figure 8-2 below shows the user inputs. They are as follows:
• Username – This is the name of the email user that is to be created. This should be between 3 and 8 characters. Spaces are not acceptable.
• Domain Name – This field is used to attach a specific domain name with the user name. All domain names on the virtual server are listed in the drop down menu. If a user does not see a domain name listed in the drop down menu, they should consult the Add Virtual Host section of this user’s guide, and confirm it has been added.
• Password – The user should ensure the password is between 6 and 8 characters, and should include both letters (upper and lower case) and numbers.
• Confirm Password – This is used to confirm that the password is correct and the same as the above password.
• FTP enabled? – This is a yes or no selection to allow this user to also have FTP access to the server.
• FTP Home Directory – This should be the path from the root of the virtual server, down to the directory that the user should have access to. Note that the FTP user will not have access to anything above the directory a user inputs here. An example of a proper home directory would be
/www/htdocs/test where the user would only have FTP access to the test directory.
Figure 8-2
Figure 8-3 below shows an error message that can often be displayed. The user name selected (‘test’) has already been created. The error states that it was created as an email alias, and because of this, the user can’t create an email alias and an email account (POP account) with the same name. The SMT will provide the user with the ability to remove the email alias, and add the email POP account or choose another POP account username.
Figure 8-3
Figure 8-4 below shows the success message for the addition of a POP Email account.
Add Mail List
This feature gives users the ability to add an email alias, which emails a group of individuals. For instance, the example in figure 8-5 below is set to show an example of the email address [email protected] to go to all the individuals that work in an office.
Figure 8-5
Why would I need to know this? This is beneficial because employees who work in the same department or for a small company can easily share information with one email address.
Add Email Addresses to a Mail List
Once the Mail List has been created (using OfficeWideEmail in this case), the user can add email addresses to the list. Each user added to the list will have to have an email address and a Real Name. Figure 8-6 below shows the form used to add email addresses to the existing Mail List. Figure 8-7 shows what the form looks like after the first user has been added.
Figure 8-7
Display List of Email Addresses in a Mail List
The “Display List” button that appears above in Figure 8-7 will display the email address and name of each individual on the Mail List, as witnessed in Figure 8-8 below.
Figure 8-8
Remove Email Address to a Mail List
To remove an email address, simply select if from the “Current Addresses” list in the drop down menu. Click the “Remove Address” button and the email address will be removed. Figure 8-9 and 8-10 below show the procedure for removing the user “Bob” from the OfficeWideEmail Mail List.
Setup Email Forwarding
In this section, users will have the ability to create email forwarding accounts. An email forward, or email alias is in essence a fake name or email address that points to a real email address, either on or off the server. There are two types of email forwards, which are outlined below.
Example 1:
[email protected] is forwarded to [email protected], where bob is a POP Email account. POP email accounts are the same as the “Email Accounts” talked about in a previous section of this User’s Guide.
Example 2:
[email protected] is forwarded to [email protected], and this address is outside of AIT’s network.
To add an Email Forward of either type listed above, complete the form as displayed in Figure 8-11 below. In this example, the Email Forward is for “webmaster”. The domain name the Email Forward is for is selected from the drop down menu. The Alias Type tells the SMT whether to setup the alias like the Example 1 above, or to set it up like Example 2.
Figure 8-11
If POP3 mail account is selected, then the user will select the POP3 email account in the Alias To input box, as Figure 8-12 shows.
Figure 8-12
If External email account is selected, then the user will enter an email address in the Alias To input box, as Figure 8-13 shows.
Figure 8-13 IMPORTANT NOTE
Email Forwarding or aliasing can be done by domain, although all domains are hosted on 1 IP address. This means that if a user has an account that allows for multiple domain names to be hosted on the account, the user can have two distinct and separate email addresses. An example of this is listed below
Example 1:
[email protected] is a POP3 email account
[email protected] is an Email Forward and sends to the POP3 account named ‘joe’.
Example 2:
[email protected] is an Email Forward.
[email protected] is an Email Forward and sends to the POP3 account named ‘joe’.
This ensures that each domain can have the same username portion of the email address, but have separate and distinct email addresses.
Configure Email Responder
The Email Responder, commonly referred to as the Auto Responder, is an email configuration that will automatically reply to email with a specific, preformatted message when a user emails a specific address.
As shown in Figure 8-14 below, the form that is used to configure the Email
Responder has many different fields. Each is detailed below, with an explanation of the information that goes into each field.
Figure 8-14
• User Name: This is just the username portion of the email address that will be used for the auto responder. For example, if the user wants people who email [email protected] to get an auto response with a preformatted message, then the field would be completed with the word ‘sales’.
• Forward Email to: This field is the email address that the email inquiry will be forwarded to. For example, if someone emails [email protected], that email will end up at the address that the user inputs. In this example, we’ve used [email protected].
• Reply Address: This field is the email address, or from address, that will be put on the reply to the person who sent the original email. For example, if someone emails [email protected], and receives the auto response, this is the email address it will be from.
• File Name: The preformatted message that is created will be a file on the server. This file will be created in the /usr/local/etc/responses directory. The file name for the auto response will be the file name that the user enters into this field. In the example above, the file name is sales.txt. This file can be edited in a simple text document.
• Email Subject: This field contains the subject line of the email that the sender will receive when they receive the auto response. For example, This is the sales information you requested.
Manage (Mail Services)
This section manages the basic email functions. Any addition function in the SMT for email can be managed in this section. Figure 8-15 below shows the default screen that appears under Manage Mail Services.
Manage Email Accounts
This section manages the POP (POP3) or mailboxes that have been added to the server. In the drop down menu, the account holder can select a username that has been created, and the Real Name and Mailbox Size will be displayed.
Clear Mail
In figure 8-16 below, you can see that the user ‘pop’ has a mailbox size of around 10KB. To clear the email out of that account without downloading it to a local computer, a user can select the “Clear Mail” button and delete the email.
Figure 8-16
Modify User
If the user selects the “Modify User” button, then it will display the form in Figure 8-17 below. This form gives users the ability to change a Password, Real Name, Home Directory (specifically for FTP, not for POP email) and the Allowed
Services, which can be POP email only, FTP only, or both POP and FTP access. Note that if providing FTP access to a user, be sure to limit their access. Normal web root or document root directories should always start with the prefix /www/htdocs. Any modifications to this path could give unauthorized users access to your website via FTP.
Figure 8-17
Delete User
Figure 8-19 below shows the results of a deletion of a user. The Results are displayed at the bottom of the page.
Figure 8-19
Manage Mail Lists
For more information on Mail Lists, see the section for Adding Mail Lists above.
Delete Mail Lists
To delete a Mail List, click on the mail list under the Existing Mail Lists heading, as seen below in Figure 8-20.
Figure 8-20
Once displayed, there will be a link that says “Delete This Mail List”. To delete the entire list, click on this link (See Figure 8-21 below). Remember, that this will delete any record of the list. There is no restore feature; a deleted list will have to be completely recreated.
Manage Email Forwarding
In this section, users can configure the default mail drop for a domain, or manage Email Forwards or Email Aliases that they have setup. Figure 8-22 shows the two options that users will have.
Figure 8-22
Configure Default Mail Drop
This section is great for users who want to have all email for a domain received by someone in an organization. For instance, assume the user has email accounts for the following 3 employees, and each of them are POP email accounts:
• Bob • Joe • Anne
After a year, Joe leaves the organization. The POP account for Joe may be removed, but an email Forward or Alias may not be set in place for Joe. If the default email drop is configured to send any email account that does not exist to Bob, then email sent to Joe will be received by Bob. In fact, email sent to addresses that don’t or have never existed will get to Bob as well.
To use this feature, click the Configure Default Mail Drop from the screen shown in Figure 8-22 above. The form listed in Figure 8-23 will display. The following fields are required to complete the default mail drop configuration.
• Alias Name: The word DEFAULT is already assumed, as this is configuring the default mail drop.
• Domain Name: This is the domain name for the default email drop. Default email drops can be setup for each domain name to go to different email addresses.
Figure 8-23
• Alias Type: The user can select POP3 account, which is a mail box account on the server in which case a drop down menu will appear with all POP email accounts in it (Figure 8-24), or External mail account, which can be an email address that is off of the user’s account (Figure 8-25).
Figure 8-24
Upon completion of the action, the Result will display at the bottom of the screen, as seen in Figure 8-26.
Figure 8-26
View Aliases
This option allows users to view the Email Forwards or Email Aliases already in place. Once the View Aliases link is clicked, the user will see Figure 8-27.
Figure 8-27
The user should click the “View Aliases” button, and the results will be displayed at the bottom of the page in the Results table shown in Figure 8-28.
Figure 8-28
To remove an Email Forward or Alias, simply click on an alias. Figure 8-29 below shows the results displayed after a Forward is removed.
Figure 8-29
Reset Anti-Relay Data File
This feature ties directly to AIT’s relay ruleset. AIT’s system of POP and SMTP services follows procedures so that a user’s POP or SMTP server cannot be exploited and used to send Unsolicited Commercial Email (UCE, otherwise known as spam). AIT’s SMTP servers are setup to give a Relaying Denied error, which is a global error that can be given by any SMTP server, or a dial up access provider. If a user receives a Relaying Denied message when attempting to send email, ensure that the user has checked their email (typically called popping for mail) before attempting to send email. If a user does this, the server will record the IP address/location where the user is dialed up FROM. This lets the server know that you are a valid user and you have authenticated with a valid username and password from the POP server.
This IP address is written into /etc/mail/relay-domains file on the Virtual Server. When you attempt to send email, the SMTP server will view the contents of this file, and find the IP address that the user is connected to and verify that this IP is the same one that is being used to send email. If so, the server will send email. If not, the sender will receive a relaying denied error.
Each night at midnight eastern time, the /etc/mail/relay-domains file is set back to nothing, or zero’ed out. The feature of resetting this file manually during the day ensures that the contents of this file are cleared.
Figure 8-30
Remove Auto Responders
Removing an auto responder or email responder is as simple as inputting the username portion of the email address in the form, and clicking the remove button.
Spam Prevention Tool
This tool allows users to block email from unwanted addresses. The address input box, shown in Figure 8-31, can contain a variety of entries specifying whose email the user wishes to refuse, including the following:
• User Address: [email protected]
• Host or Domain Name: host01.spam.com OR spam.com • IP Address: 123.123.123.123
Figure 8-31
Upon addition of an email address, IP address or host name, the results will display, as seen in Figure 8-32 below.
FTP Services
FTP, or File Transfer Protocol, services are for users who wish to upload data to the server. Usually, this data is web files for websites, such as images (i.e. .jpg or .gif files) or HTML, Perl or PHP files. This section will help users create, and manage FTP options, including adding FTP users, anonymous FTP access, and welcome messages. The main screen of the FTP services section is the “Add” interface, and should look something like what is displayed in Figure 9-1.
Figure 9-1
Create FTP Account(s)
To create an FTP account, simply click on the Create FTP Account link and complete the form, displayed in Figure 9-2 below. Complete the form displayed, including the following information in the form.
• Username – This is the username, between 3 and 8 characters, which the user will connect with. The username should be in all lower case, and must be unique to the virtual server.
• Domain Name – This should be the domain name that the FTP account is for.
• Real Name – This section should include the user’s real name for tracking purposes.
• Password – As in any web service, the password MUST be between 6 and 8 characters, and SHOULD contain letters and numbers. For security reasons, do not use passwords like love, password, or 123456 for security reasons. • Confirm Password – This MUST match the password from above.
• POP3 Mail Enabled – This option sets the FTP account as a POP3 or POP email account. This can be seen in the Manage Email Accounts section. • FTP Home Directory – This option sets the FTP home directory for the user.
This user will only be able to see the directories and files below the Home Directory. Meaning, if the user puts “/” in the Home Directory input box, then that FTP user will have root access to the virtual server. If the user puts “/www/htdocs” then the FTP user will have access only to /www/htdocs, and nothing above it. For FTP access for virtual host domains, it is recommended to use /www/htdocs/vhdir where vhdir is the directory name for the virtual host domain name.
Figure 9-2
The success message, displayed below in Figure 9-3, should show that the user was successfully added.
Figure 9-3
Setup Anonymous FTP
Anonymous FTP accounts will be created by the user if he wishes to allow his customers to ftp to his server without the use of a username or password.
NOTE: This option is a security risk as it does not limit the amount or type of data uploaded to the server.
To enable Anonymous FTP, enter the path to the directory for which you wish to allow anonymous ftp access. Figure 9-4 below shows an example of the form.
• Anonymous FTP Directory – This option sets the FTP home directory for anonymous access. The user will only be able to see the directories and files below the Anonymous FTP Directory. Meaning the Anonymous FTP user will have root access to the virtual server. If the user puts “/www/htdocs” then the FTP user will have access only to /www/htdocs, and nothing above it.
Figure 9-4
The success message, displayed below in Figure 9-5, should show that the Anonymous ftp directory was successfully added.
Figure 9-5
Disable Anonymous FTP
To disable an Anonymous FTP account, the user will need to input the path of the current Anonymous FTP Directory. Click the button labeled “Disable”. This will disable anonymous access to the specified directory.