Selecting the Best Development Technology for Your Application Development Scenario
Full text
Figure



Related documents
Technical questions concerning this Request for Proposal should be directed to Pauline Williams, Information Specialist at the Gainesville Area Chamber of Commerce via email at
Experiments with the energy harvester fitted with steel plectra produced by photochemical machining focused on the comparison of power produced with walking gait (Figure 7) and
A notion of AKE-security for AB-AKE is presented based on the security models for group key exchange protocols and also taking into account the security requirements
Then you may post the shipment by clicking the button Posting/Ship transfer order. In the upper pane of the Shipment posting form, choose “All” in the column Update and select the
Omani banks that have foreign branches are required to translate their assets, liabilities and income statements into Omani rials at the rates of exchange at the balance sheet date..
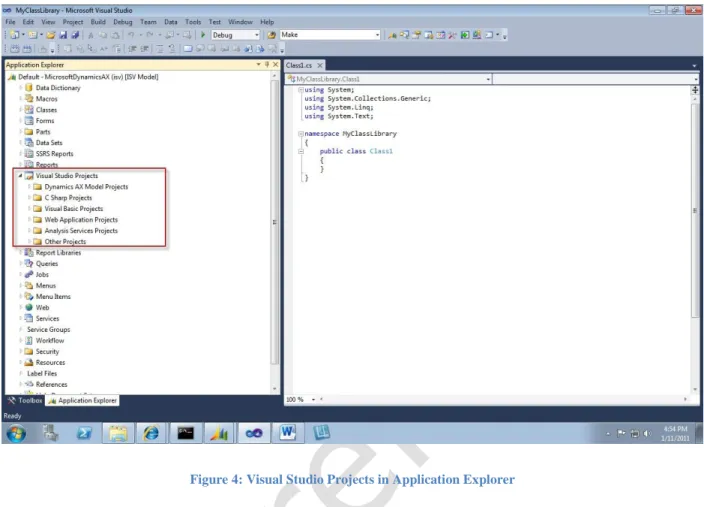
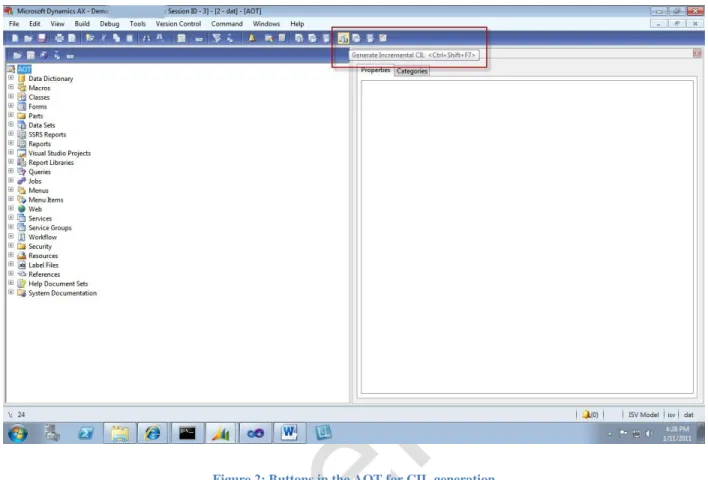
This module introduces the features in Microsoft Dynamics AX 2012 that support the sales and purchase processes, and it also reviews the data models and coding patterns for many of
If the Microsoft Dynamics AX client is not deployed with attention to security, then malicious users might gain access to Microsoft Dynamics AX data, or users in your business
This study used both common and rare variants, using polygenic and pathway analyses, to evaluate the genetic etiology of ADHD in a large homogenous Han Chinese case–control