Appendix B Network, Routing, Firewall, and Basics
Full text
Figure


Related documents
Ten years into the reign of Thorin the First, son of Thráin the Old, the King resolved to remove the royal house of Durin’s folk from Erebor to abide in the Grey Mountains.. At the
Step 1: Draw the configuration diagram.. • Problem 11: For the mechanism shown in figure link 2 rotates at constant angular velocity of 1 rad/sec construct the velocity polygon
The Single Firewall Policy and Double NATing Firewall Rules solution has the limitation that it only opens up access to the public address of the server(s) for certain private hosts
youngsters and the women to buy scooters Major players in the 2- wheeler industry are Hero Honda Motors Ltd (HHML), Bajaj Auto Ltd (Bajaj Auto) and TVS Motor Company Ltd (TVS)..
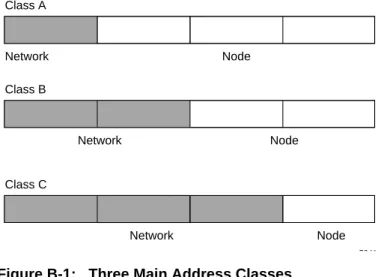
2-4 TCP/IP Networking Basics For each unique value of the network portion of the address, the base address of the range (host address of all zeros) is known as the network address
If the network number is a valid network number, the subnet number is a valid subnet number and the host number is all ones, then the address refers to all hosts on the
ATMOSPHERIC ATMOSPHERIC PRESSURE SENSORS PRESSURE SENSORS ENGINE ENGINE CONTROL CONTROL LOGIC LOGIC THROTTLE THROTTLE SHUTDOWNS SHUTDOWNS ENGINE RPM ENGINE RPM TDC TDC 6 6 5 5 4 4 3 3
The TEGIVS project has created a national model for preparing future teachers for Virtual Schooling (VS), or K-12 distance learning, and in particular to prepare all future
