Recommendations and evidence for reporting items in pediatric clinical trial protocols and reports: two systematic reviews
Full text
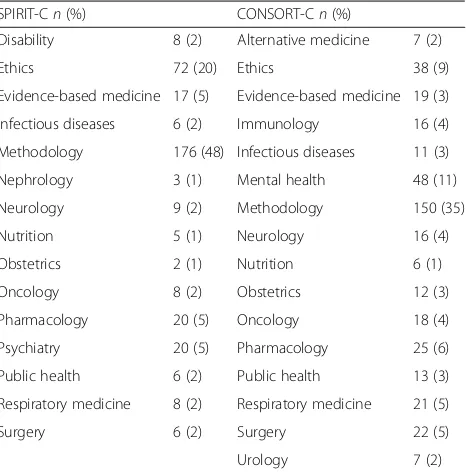
Figure



Related documents
• If the attacker tries the same username twice within one year and gets different salts, then he learns that either the username is not in the database and the current σ has
security, applications and operating systems to keep the internet as a secure channel to exchange.. information by reducing the risk
T V Reddy: Primarily a poet is a poet, not a social reformer or preacher. He writes to express his feelings and thoughts. However, a poet is a member of the society and
From single term concatenated with synonym and generates N-gram consecutive made TD features return good and significant clustering result. As we mentioned previously in
Surface reconstruction is completed in reverse engineering based on CATIA V5, It sets up the shrimp solid model realistically, and then completed the design of
Hence, our main aim is to investigate the Ekman boundary layer mixed convective heat transfer steady flow past a continuously moving semi-infinite vertical plate
Mohd Hairy Mohamaddiah [6], conducts a survey study about resource monitoring and allocation in cloud computing environment. Cloud providers supply various