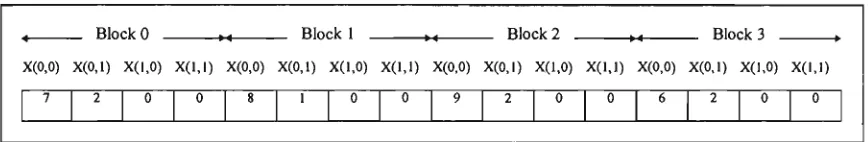
Digital image transformation and compression
Full text
Figure


Related documents
The encryption operation for PBES2 consists of the following steps, which encrypt a message M under a password P to produce a ciphertext C, applying a
proyecto avalaría tanto la existencia de una demanda real e insatisfe- cha de este servicio por parte de la población titular de derechos como la capacidad de ambos
The projected gains over the years 2000 to 2040 in life and active life expectancies, and expected years of dependency at age 65for males and females, for alternatives I, II, and
This essay asserts that to effectively degrade and ultimately destroy the Islamic State of Iraq and Syria (ISIS), and to topple the Bashar al-Assad’s regime, the international
Heather gave a speech, Paul performed a number from his forthcoming album and some films about landmines were screened, including Heather's film with Paul's
Further, by showing that v τ is a modular unit over Z we give a new proof of the fact that the singular values of v τ are units at all imaginary quadratic arguments and obtain
National Conference on Technical Vocational Education, Training and Skills Development: A Roadmap for Empowerment (Dec. 2008): Ministry of Human Resource Development, Department
(Although basic math facts include addition, subtraction, multiplication, and division, this study tested multiplication only.) The students’ fluency was then related to their

![Fig. 7-3 Arithmetic coded example for the sequence fE, A, I, I, !} [WIT87].](https://thumb-us.123doks.com/thumbv2/123dok_us/7921409.1315306/136.549.26.477.183.363/fig-arithmetic-coded-example-sequence-fe-i-wit.webp)