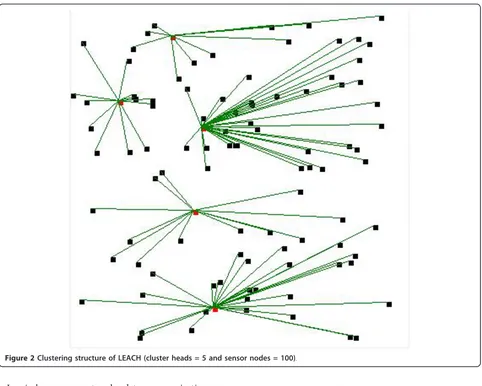
An efficient cluster based power saving scheme for wireless sensor networks
Full text
Figure


Related documents
In asymmetric-key cryptography different keys are being used for both encryption and decryption.Hash is an algorithm where a block of data is taken and fixed size bit
The in-plane response for control (ambient) and heated specimens will be compared to investigate the effects of accident thermal loads on the stiffness, peak strength and
The purpose of this study was to ascertain and understand the viewpoints of enlisted Army and Marine Corps veterans toward the transitional process into higher education
RESEARCH Open Access Human herpesvirus 8 in northwestern China epidemiology and characterization among blood donors Xing Wang1, Bin He2, Zhaoxia Zhang1, Tao Liu1, Hui Wang1, Xu Li3,
P?the et al Earth, Planets and Space (2014) 66 162 DOI 10 1186/s40623 014 0162 2 FULL PAPER Open Access Reproducing electric field observations during magnetic storms by means of rigorous 3
This article discusses the alleged ill effects of long working hours, before digging below the surface debates to look at time itself in more detail. It argues that we experience
primeras líneas, toda la narrativa —tanto la alegoría como la ironía de Doña Perfecta!. Este texto liminar lo componen los dos primeros capítulos de la novela, y toda
diabetic neuropathy in control.Our Cortex-feet foot analyzer and blood flow stimulator will be having.. hand-held unit which can be integrated to a wrist watch and a foot-unit which