AN EFFICIENT INFORMATION RETRIEVAL SYSTEM USING QUERY EXPANSION AND DOCUMENT RANKING
Full text
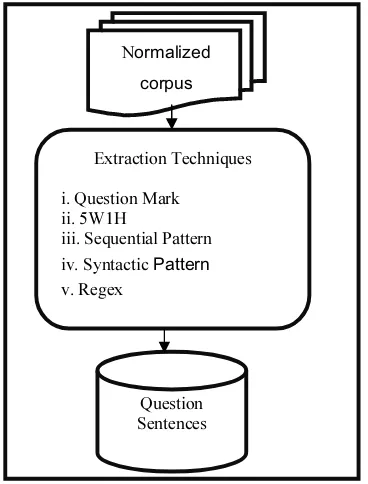
Figure



Related documents
So to prevent unauthorized access through hacking we are using cryptography with additional technique known as LDPC encoder and Stopping sets to make the basic
These learning experiences imply both changes in personal practice and the development of collective action, both of which are discussed in more detail below.
(2007) 'Criteria for evaluating research: the unique adequacy requirement of methods,' Construction Management and Economics,..
Institute of Civil Engineers (1991) CESMM 3: Civil Engineering Standard Method of Measurement,. (third edition) Thomas
Linking these two functions together are the feedback packets exchanged between ingress and egress routers; ingress routers send egress routers forward feedback packets
Microsoft Word StudentHealthServices 0607 AR doc DELTA STATE UNIVERSITY NON ACADEMIC ANNUAL REPORT Academic Year 2006 07 I Unit Title O W Reily Health Services Division or
present study the Eudrilus eugeniae were grown in cow dung and their life cycle were studied in.. different days of intervals like 15, 30,45 and
