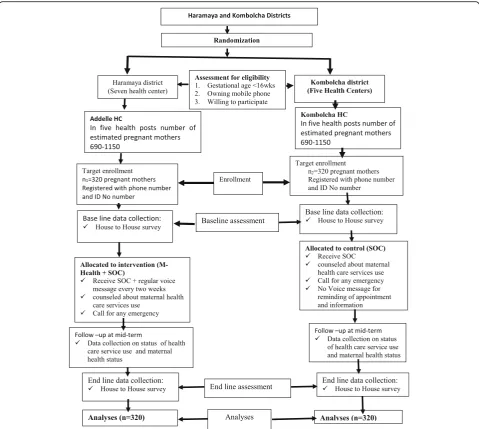
Effect of Mobile health on maternal health care service utilization in Eastern Ethiopia: study protocol for a randomized controlled trial
Full text
Figure


Related documents
health searches on ADR reporting (January 1997 to August 2007) including cross-referenced articles. Twenty-four out of 260 eligible studies were identified and critically
vulnerable to dictionary attacks. Users also suffer from password reuse attacks. In OPASS the attacker can steal a user’s cell phone to log on websites. 2) Server side:.. The
Very recently, Li [] presented an LQP-based prediction-correction method: the new iterate is obtained by a convex combination of the previous point and the one generated by
The design idea of the dynamic RO unit based on the mesh model proposed in this paper can generate a variety of oscillation frequency and path deadlock, which makes the PUF's
Noor, KI, Ahmad, QZ, Noor, MA: On some subclasses of analytic functions defined by fractional derivative in the conic regions. Noor, KI, Fayyaz, R, Noor, MA: Some classes of k
Low disclosure rates in this study could also be attrib- uted to family caregiver lack of disclosure related know- ledge and skills as well as the low involvement of health
While under physiological conditions the number of mela- nocytes in the oral epithelium is the same regardless of racial/ethnic origin [1], the colour of oral mucosa varies