Non Traveling Wave Solutions for the (2+1) Dimensional Breaking Soliton System
Full text
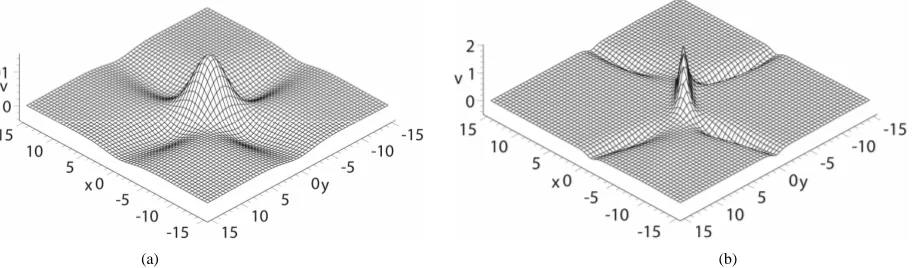
Figure
Related documents
The coverage planning used to obtain the LTE cell range is based on the required receiver sensitivity, and link budget calculations to estimate maximum allowable path
Although identity management has many aspects to it (e.g. prevention of identity theft or development of authentication requirements), we concentrate on the issue of
To test if exogenously added TWEAK also preferentially activated the non-canonical NF-κB pathway in B16 cells, the empty-vector V1 cell line was treated with recombinant
FIGURE 4 Effect of sphingomyelin concentration on the activation of lysosomal sphingomyelinase by apoC mixture and LPC.. Assays were conducted as described in Methods, using 12 ,g
Eight dogs from western Washington State suspected of being infected with Anaplasma phagocytophilum because of the finding of morulae in peripheral blood neutrophils were studied
Crime Generators: Places that bring people together and create crime opportunities for offenders who also happen to be there (e.g. a bus terminal, a school). Crime
This thesis focuses on the international-domestic interaction within the context of the 1908 Ottoman Constitutional Revolution and examines it in relation to the
Compensation for adopting forest certification = f (Sociodemographic, Ownership size, Tenure, 141.. Acquisition Mode, Management Objectives, Harvest history, Owners Familiarly