Access Control and Encryption of Sensitive Data Using i-Se4GE Algorithm
Full text
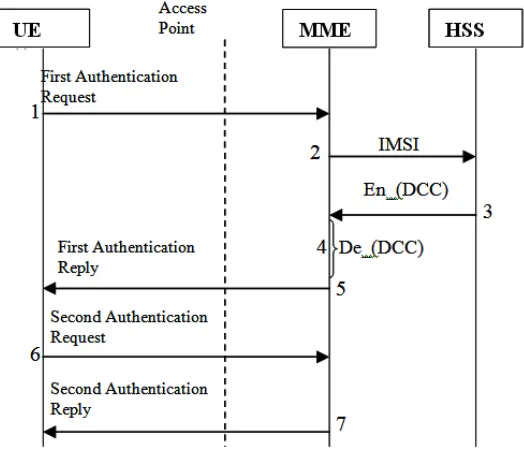
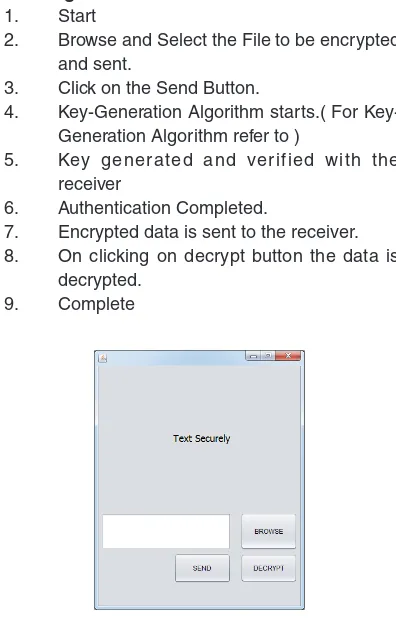
Figure
Related documents
• Enables mobile users to send and receive encrypted messages directly on their mobile device. • IT administrators can easily provision and manage users
By the result of Bernstein, the canonical points of spaces of polynomials are explicitly known. See Theorem 4.5 from the chapter about polynomial interpolation... 5.3 Best L 1
To do this, I rely here upon the work of Giorgio Agamben on the powers of language, and I will give a brief exegesis of three crucial moments in Agamben’s work
Se logró observar que el sector posee fechados radiocarbónicos ubicados desde el Holoceno medio hasta el Holoceno tardío, que se alejan de algunas interpretaciones que
BMP al- lows subscribers to send and receive text, voice and video messages; attach photos; manage contact lists; and schedule and manage conference calls.. To access BMP via
The guard tour software allows users and dispatcher to send text messages. The dispatcher can decide to convert text message in
Three different film coating formulas, Opadry ® , complete film coating system (03F18435), Opadry ® II, high performance film coating system (85G18490) and Opadry amb,
Available in oil-only, universal and chemical versions , spill kits are essential for industrial manufacturing facilities, transport and shipping companies, pipelines, gas stations