RELATIONSHIP BETWEEN INFORMATION SECURITY AWARENESS AND INFORMATION SECURITY THREAT
Full text
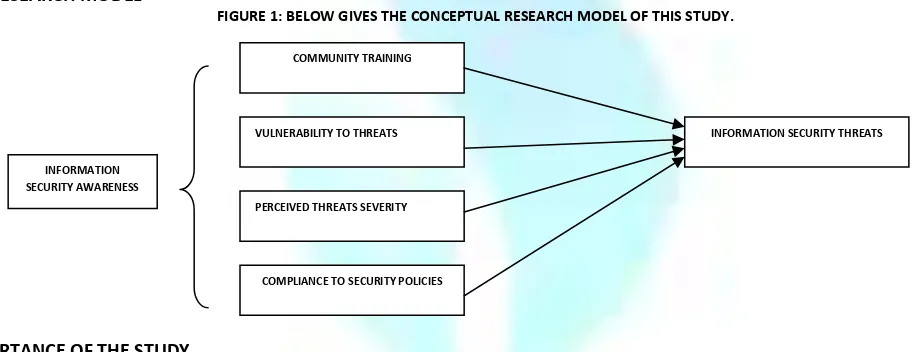
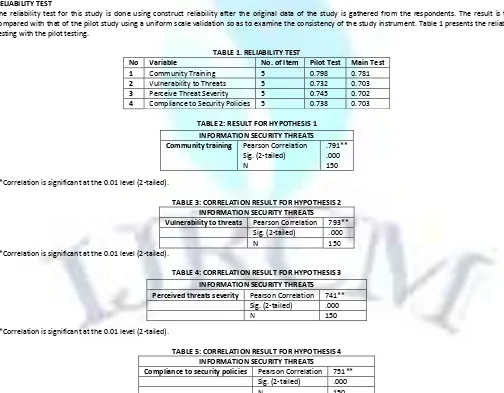
Figure
Related documents
Wife’s evidence included a return of service indicating that the amended show cause order and sworn petition were served on husband’s mother-in-law at the Washington address
While there is no statutory definition for “data brokers,” the Federal Trade Commission (FTC) has defined this term to include “companies that collect information, including personal
As an example of the applications, a high gain planar array antenna at V band by using the half-height-pin gap waveguide has been designed and is presented in the paper with a
In MS-AR models, several autoregressive models are used to describe the time evolution of the series and the switching between these different models is controlled by a Hidden
Gait analysis using gravitational acceleration measured by wearable sensors. A practical gait analysis system
communicate using proper framing terminology. Define and use terminology related to wall framing. Identify and collect materials and tools needed to complete the assignment.
concurrency control, recovery management, lock mechanism, compensation, long-term transactions, service-oriented architecture, consistency, recoverability, partial results,
Also, we have presented a load-sharing policy for the case of speculative PDES execution with both cross-state and message-exchange interactions, which has revealed effective with