Verifiable Delegation of Computation through Fully Homomorphic Encryption
Full text
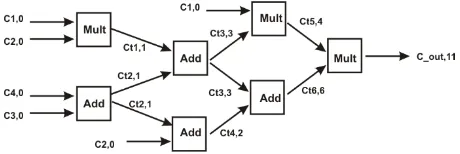
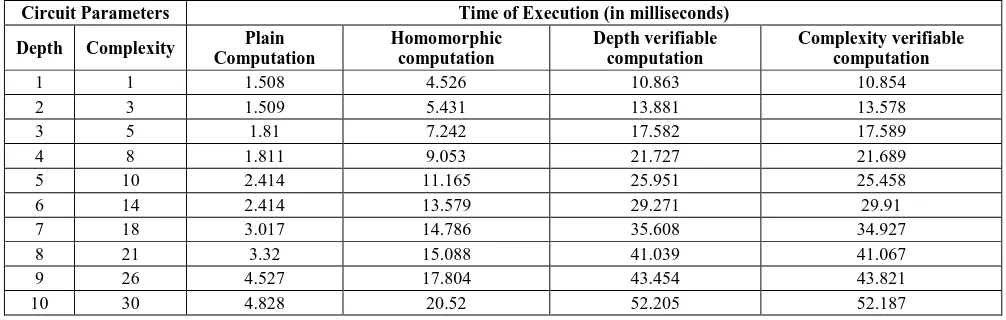
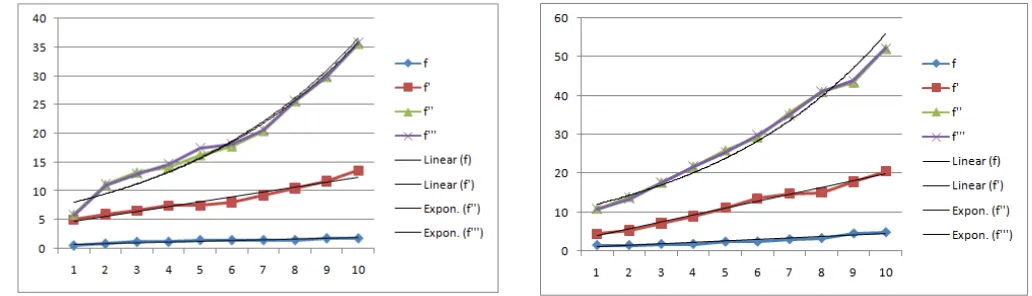
Figure
Related documents
These data highlight current practice patterns in EDs associated with pediatric train- ing programs and may assist in the development of prac- tice standards for pediatric
From the experimental evaluation we conducted on the PMS and WPMS instances at the 2012 MaxSAT Evaluation, we can conclude that the new approach is both the best performing
òN÷í8î4òþDïCøô-ôYü4ó8ù8ñDïCù ñrìD E)òÔõïAðNïAîF)ô4ñdì8ûïRñdüñdôúNô4ïCù
Therefore, the purpose of this study was to determine the uptake of contraceptive services, the characteristics of contraceptive acceptors and the trends in
The load-deflection comparison of the phase I test specimens shows that the test specimens strengthened with the high tensile CFRP strands have a higher deflection at failure compared
In phage X, when DNA replication is blocked, recombination mediated by the Red pathway occurs only near the double-chain break site, cos, that defines the termini of the
Gouget, An upper bound on the number of m -resilient Boolean functions, ASIACRYPT 2002, Lecture Notes in Comput. Klapper, Upper bounds on the number of resilient
tracing specific aspects of Canadian history, society, and pop culture from Canada’s earliest days to current times, I attempt to uncover the “true origins” of the