Volume 2, Issue 3, 2015
60 Available online at www.ijiere.com
International Journal of Innovative and Emerging
Research in Engineering
e-ISSN: 2394 - 3343 p-ISSN: 2394 - 5494
Image Encryption using MATLAB with Hybrid Method
Neha Mistry
a, Hiral Davda
a, Helina Patel
aaStudent of Electronics & Communication GEC/GTU Bharuch, Gujarat, India
ABSTRACT:
The main purpose of developing a digital image encryption technique is to satisfy both imperceptibility and robustness requirement. Digital encryption appear as an efficient means of securing multimedia contents such as copyrighting protection and image authentication. The key aspects some encryption and decryption techniques are robustness and tampering proofing. In this paper robustness is improved through combination of discrete wavelet transform and singular value decomposition method. DWT is used for decomposition of image into sub bends which gives linear flexibility of images in terms of scalability, resolution and distortion.
By adding SVD along with DWT, peak signal to noise ratio can be improved. Results is analysed by MATLAB.
Keywords: Digital Images, DWT, SVD, MATLAB, Embedding, Extracting
I. INTRODUCTION
With the advent of digital techniques, most of the data (image, audio and video) is stored in digital form which offers many advantages. Along with the advantages, some of the major drawbacks that a user can face are the untroubled copy of data without any degradation in the quality. Due to the ease in copy and distribution of the digital content, for an average user them modification of the copied data was at hand. The sharing of digital content over the internet is a very common practice. Therefore a system which would protect the digital content so that its copyright is secured was required. Encryption and decryption technology developed for copyright information is embedded inside the original images, which is to be protected from the illegal replication. Robust watermarks are designed to resist any modifications and design for copyright protection. Fragile watermarks are designed to fail whenever the cover work is modified and give some measure of tempering. Fragile watermarks are used in authentication. The fragile watermarks can be embedded in either the space domain or frequency domain of an image.
II. RELATED WORK
A. Practical Model:
π
I I<π> I<a> <W>
Attack
K K
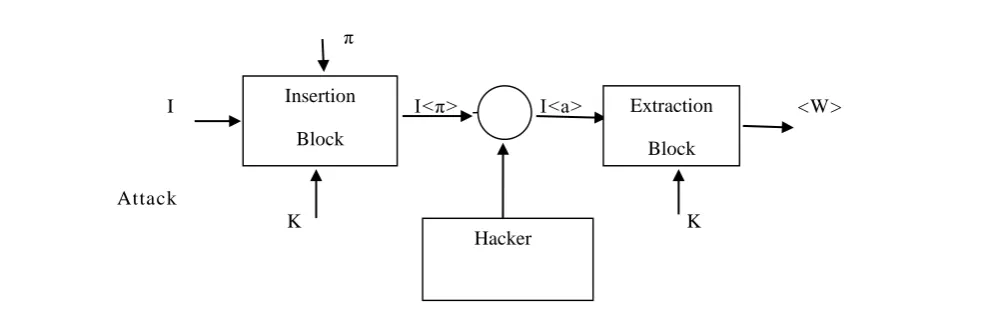
Figure 1. General Encryption System
A generalized watermarking system may be devised in fig1. In the Watermark Insertion Block, copyright information is hidden inside the original piece of work in an encrypted form the original image, I is processed inside this watermark insertion system.
The other input to this block is the copyright information or the watermark, W to be embedded inside I using the secret key, K. Thus, the final image available in the market is a composite image, Iw containing the encrypted logo inside the original image. This composite image available in the market has every possibility of being attacked by the hackers in a bid to destroy the watermark embedded inside it, to generate the hacked version, <Iw> of the composite image. Once the
Insertion
Block
Extraction
Block
Volume 2, Issue 3, 2015
61 hackers become successful in destroying the watermark the original piece of work becomes susceptible to all kinds of fraud.
The primary aim of the Watermarking Extraction Block is to successfully extract an estimate of the copyright information, <W> from the hacked version <Iw>. The better the watermarking system the more <W> resembles W[1].
B. Types of Technique:
Digital encryption and decryption techniques can be categorized into one of the two domains, according to the embedding domain of the host image[2].
1) Spatial domain 2) Frequency domain
1)Spatial domain
Here pixels are taken into consideration which means host image pixels are embedded on cover image pixels. The oldest and the most common used method in this category is the insertion of the watermark into the least significant bits (LSB) of pixel data.
2) Frequency domain
In frequency (transform) domain technique transform coefficient is taken into consideration means the information is embedded into cover image by altering its transform coefficient. This is robust watermarking with respect to the spatial domain technique the different transform domain technique that are as follows: 1) DFT. 2) DCT. 3) DWT. 4) SVD[3].
III.DWTANDSVD
A. Discrete Wavelet Transform (DWT):
Wavelet domain is a promising domain for watermark encryption. Wavelet refers to small waves. Discrete Wavelet Transform is based on small waves of limited duration and varying frequency[4]. This is a frequency domain technique in which firstly cover image is converted into frequency domain and then its frequency coefficients are modified in accordance with the transformed coefficients of the watermark and watermarked image is obtained which is very much robust. DWT decomposes image hierarchically, providing both spatial and frequency description of the image. It decompose an image in basically three spatial directions like horizontal, vertical and diagonal in result separating the image into four different components namely LL, LH, HL and HH. Here first letter refers to applying either low pass frequency operation or high pass frequency operations to the rows and the second letter refers to the filter applied to the columns of the cover image. LL level is the lowest resolution level which consists of the approximation part of the cover
image, LH, HL, HH give the detailed information of the cover image. For second level of decomposition any one sub-band is selected and is further decomposed into four levels. Maximum the level of decomposition, maximum will be the robustness of the watermarked image. At every level of decomposition, the magnitude of DWT coefficient is larger in lower bands (LL), and is smaller in other three band (LH, HL, and HH). HVS (Human Visual System) is more sensitive to the low frequency parts (the LL sub-band), so encryption or decryption is preferably placed in other three sub-bands to reconfigure the quality of original image.
B. Singular Value Decomposition (SVD) :
Singular Value Decomposition transform is a linear algebra transform which is used for factorization of a real or complex matrix with numerous applications in various fields of image processing[5]. As a digital image can be represented in a matrix form with its entries giving the intensity values of each pixel in the image, SVD of an image N with dimensions n x n is given by:
N = USVT Where,
U and V = orthogonal matrices ,S =singular matrix ,
It is a diagonal matrix carrying non-negative singular values of matrix N. The columns of U and V are called left and right singular vectors of N, respectively. They basically specify the geometry details of the original image. Here U represents the horizontal details and right singular matrix , and V represents the vertical details of the original image. The diagonal values of matrix S are arranged in decreasing order which signifies that importance of the entries is decreasing from first singular value for the last one, this feature is employed in SVD based compression technique. There are two main properties of SVD to employ in digital watermarking schemes[6]:
1. Small variations in singular values does not affect the quality of image and,
Volume 2, Issue 3, 2015
62
IV.PROPOSED WORK
(a)
(b)
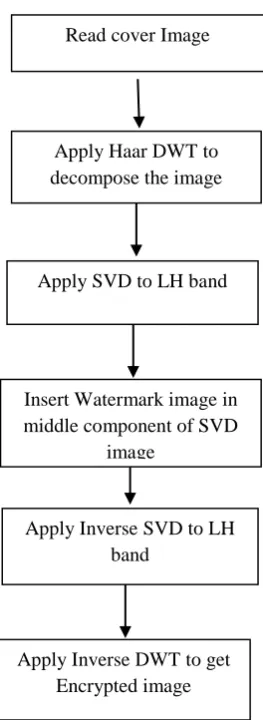
Figure 2. (a) Encryption algorithm (b) Decryption algorithm
The image decomposition is done with “Haar” which is symmetric, simple and orthogonal wavelet. The SVD is then applied to a selected sub band. This result in three matrices U, S and V. We assume the dimension of the cover image I is N x N.
A. Encryption Process:
Read the cover image of size and the watermark of the same size.
Use Haar DWT to decompose the image into four sub bands like ( LL, LH, HL, HH ) Apply SVD to LH sub-band i.e. Io = Uo*So*Vo*T ,Where Io = LH
Insert the watermark image into the middle component of the SVD applied cover image as in above equation: E = Ue*Se*Ve*T
Where E = encryption
Apply inverse SVD to the LH sub-band by multiplying the modified matrix So E with the orthogonal matrices. Apply inverse DWT to get the encrypted image.
B. Decryption Process:
Read the watermarked image.
Apply Haar DWT to decompose the encrypted image into four sub-bands i.e. ( LL, LH, HL, HH ) Apply SVD to LH sub-band i.e. Ioe = Uoe*Soe*Voe*T
Where Ioe = LH
Read Watermarked Image
Apply Haar DWT to decompose the image
Apply SVD to HL band
Original image is computed using middle component of
SVD and decrypted the image
Apply Inverse SVD
Apply Inverse DWT
The Original image is recovered Read cover Image
Apply Haar DWT to decompose the image
Apply SVD to LH band
Insert Watermark image in middle component of SVD
image
Apply Inverse SVD to LH band
Volume 2, Issue 3, 2015
63 The matrix as the middle component of the SVD that includes the orignal image is computed and it is decrypted using
the original image as it is a non-blind watermarking method. Apply inverse SVD to the LH sub-band.
Perform inverse DWT method. The original image is recovered.
C. Performance Parameter 1. PSNR:
The quality of decrypted image can be measured by PSNR(peak signal to noise ratio) .PSNR is provided only to give us a rough approximation of the quality of watermark.[4]
PSNR = 10 log10 (255/MSE)2
MSE=∑ ∑ (𝑎𝑖𝑗−𝑏𝑖𝑗)2
𝑛∗𝑚 𝑚−1 𝑗=0 𝑛−1 𝑖=0
Where, m x n is the image size, and are the corresponding pixel values of two images.
V.EXPERIMENTAL RESULTS
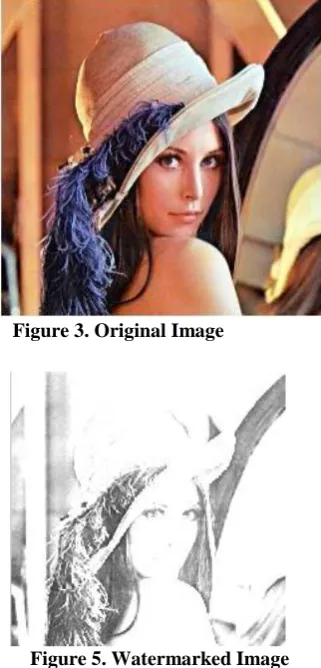
To demonstrate the proposed approach, Lena’s image is used as an original image and copy-right image is used as the watermark. Figure:1 shows the cover image of size 512 x 512. Figure:4 shows the watermark image of size 340 x 340. Figure:5 shows the watermarked image. Figure:6 shows the recovered watermark image.
Figure 3. Original Image Figure 4. Watermark Image
Figure 5. Watermarked Image Figure 6. Recovered Watermark image
The PSNR was used as a measure of the quality of a watermarked image.
Table 1 shows the peak signal to noise ratio mean square error of our proposed method of original image with various watermark image, where our watermarked images PSNR has a better performance than others.
Table1. Experimental Data Original
Image
Watermark Image
MSE PSNR
Lena Image
Copy right Image
Volume 2, Issue 3, 2015
64 Lena
Image
Mission Completed Image
0.0258 63.8415
VI. ADVANTAGES
Enhance security. Data can be secure. Improve quality of image.
Tamper detection and localization. Copyright protection.
Discourage thieves.
VII.DISADVANTAGES
Limited protection. Time Consuming.
VIII.APPLICATION
Annotation and privacy control. Media forensics.
Broadcast monitoring. Device control. Copy control.
Communication enhancement.
VIII.CONCLUSIONS
Watermarking (encryption and decryption) is an information hiding technique where a secret or personal information is concealed in the digital content. In order to make this hidden information secure, imperceptible and robust, the watermark should be embedded in some proper locations. Improving the security aspect of the watermarking system, without any cost of imperceptibility and robustness, is one of the challenges of nowadays research in watermarking.
In our simulation we go through the numerous tests on original image with size 512 x 512. In our proposed method , PSNR of watermark images values are high as compare to other papers. The experimental results have confirmed that this hybrid technique has two properties like high fidelity and robustness..
ACKNOWLEDGMENT
It is honour and pleasure to express my heartfelt gratitude to those who helped me and also contributed towards the preparation of this seminar. I am indebted to my guide Prof M.A. JAJAL &.S.J. DAWDA, whose invaluable guidance and timely suggestion and constructive encouragement inspired me to complete the project in the present form. I express my thanks to the Library of Government Engineering College, Bharuch. which is a source of such invaluable information and of course the Internet Facility of the same. I would like to thank to the entire team of B.E. Staff whose direct and indirect suggestion helped me creating this project. I would like to pay a special thanks to my parents for the sparing their invaluable time and inspiring me. Although there remain some names but none are remain un-thanked.
REFERENCES
[1] H.T.Wu and Y.M.Cheung,"Reversible watermarking by modulation and security enhancement ,"IEEE Trans. Meas.,Vol.59 no.1,PP.221-228,jan 2010.
[2] Won-Gyum Kim,Chan-woo Lee ,Won Don Lee,"A waremarking Scheme for both spatial and frequency domain to extract the seal image without the original image",IEEE Signal Processing Magazine in 1999.
[3] Sakshi Verma and Shashank Chakrwarti ,"digital Watermarking", international journal of information and computation technology,vol-4,PP 1291-1298,Number 13(2014).
[4] Chunlin Song, SudSudirman, MadjidMerabti, “Recent Advances and Classification of Watermarking Techniques in Digital Images”, ISBN: 978-1-902560-22-9 © 2009 PGNet
[5] Manjunath. M, Prof. Siddappaji, “A New Robust Semi blind Watermarking Using Block DCT and SVD”, IEEE International Conference on Advanced Communication Control and Computing Technologies (ICACCCT), pp. 193- 197, 2012.
[6] L. Demanet, “ Curvelets, wave atoms, and wave equations”, Ph.D. thesis, Caltech, 2006.