CSEIT1183176 | Received : 05 Jan 2018 | Accepted : 19 Jan 2018 | January-February-2018 [(3) 1 : 261-267 ]
International Journal of Scientific Research in Computer Science, Engineering and Information Technology © 2018 IJSRCSEIT | Volume 3 | Issue 1 | ISSN : 2456-3307
261
Provable Multicopy Dynamic Data Possession in Cloud
Computing Systems
T. Swetha Singh1, M. Venkateswara Rao2
1M.Tech Scholar, Department of CSE, Vignana Bharathi Institute of Technology Aushapur (V), Ghatkesar (M), R.R., Telangana, India
2Asstistant Professor, Department of CSE, Vignana Bharathi Institute of Technology Aushapur (V), Ghatkesar (M), R.R., Telangana, India
ABSTRACT
Continuously a regularly expanding number of affiliations are picking outsourcing data to remote cloud pro associations (CSPs). Customers can rent the CSPs accumulating establishment to store and recuperate for all intents and purposes endless measure of data by paying costs metered in gigabyte/month. For an extended level of versatility, availability, and strength, a couple of customers may require their data to be recreated on various servers over different server ranches. The more copies the CSP is made a demand to store, the more costs the customers are charged. Along these lines, customers require a strong confirmation that the CSP is securing all data copies that are settled upon in the organization contract, and each one of these copies are unsurprising with the most recent modifications issued by the customers. In this paper, we propose a guide based provable multicopy dynamic data possession (MB-PMDDP) plot that has the going with features: 1) it gives a proof to the customers that the CSP isn't hoodwinking by securing less copies; 2) it supports outsourcing of dynamic data, i.e., it supports square level operations, for instance, piece change, incorporation, deletion, and add; and 3) it empowers affirmed customers to faultlessly get to the record copies set away by the CSP. We give a relative examination of the proposed MB-PMDDP plot with a reference show procured by extending existing provable responsibility for single-copy designs. The theoretical examination is endorsed through exploratory results on a business cloud arrange. Similarly, we show the security against interesting servers, and discuss how to perceive defiled copies by to some degree changing the proposed plot.
Keywords :Cloud Pro Association, MB-PMDDP, PDP
I.
INTRODUCTION
Outsourcing data to a remote cloud expert center (CSP) empowers relationship to store a more noteworthy number of data on the CSP than on private PC structures. Such outsourcing of data accumulating engages relationship to concentrate on advancements and soothes the heaviness of enduring server revives and other handling issues. Likewise, many embraced clients can get to the remotely set away information from various geographic zones making it all the more pleasing for them.
degree deleted after some time. Consequently, various researchers have focused on the issue of provable data possession (PDP) and proposed unmistakable plans to audit the data set away on remote servers.
II.
LITERATURE SURVEY
1) A privacy-preserving remote data integrity checking protocol with data dynamics and public verifiability
Authors: Z. Hao, S. Zhong, and N. Yu
Remote data uprightness checking is an essential advancement in appropriated processing. Starting late, many works focus on giving data components and in addition open undeniable status to this sort of traditions. Existing traditions can reinforce the two features with the help of a pariah evaluator In a past wor , Se et al propose a re ote data trustworthiness chec ing tradition that support data strea In this paper, we change Se et al s tradition to help open unquestionable status. The proposed tradition supports open conspicuousness without help of an untouchable commentator. Moreover, the proposed tradition does not discharge any private information to pariah verifiers. Through a formal examination, we exhibit the exactness and security of the tradition. Starting now and into the foreseeable future, through speculative examination and trial comes to fruition, we show that the proposed tradition has a better than average execution. accumulating organization. In this paper, we propose a pleasing provable data proprietorship plot in cross breed fogs to help flexibility of organization and data development, in which we consider the nearness of various cloud expert centers to supportively store and keep up the clients' data. Our tests show that the
affirmation of our arrangement requires a little, predictable measure of overhead, which limits correspondence diserse quality.
III.
EXISTING SYSTEM
1. Once the data has been outsourced to a remote CSP which may not be trustworthy, the data proprietors lose the prompt control over their delicate data. This nonappearance of control raises new extensive and testing errands related to data mystery and trustworthiness protection in conveyed figuring. The arrangement issue can be dealt with by encoding sensitive data previously outsourcing to remote servers. In that limit, it is a vital demand of customers to have a strong confirmation that the cloud servers still have their data and it isn't being adjusted or to some extent deleted after some time. Consequently, various pros have focused on the issue of provable data proprietorship (PDP) and proposed unmistakable plans to audit the data set away on remote servers.
2. One of the middle arrangement models of outsourcing data is to give dynamic direct of data to various applications. This suggests the remotely set away data can be gotten to by the endorsed customers, and also revived and scaled (through square level operations) by the data proprietor. PDP designs presented focus on simply static or warehoused data, where the outsourced data is kept unaltered over remote servers. Instances of PDP improvements that plan with dynamic data. The last are however for a lone copy of the data record.
IV.
PROPOSED SYSTEM
2. We propose a guide based provable multi-copy dynamic data possession (MB-PMDDP) plot. This arrangement gives an adequate confirmation that the CSP stores all copies that are settled upon in the organization contract. Also, the arrangement 3. reinforces outsourcing of dynamic data, i.e., it supports square level operations, for instance, piece change, incorporation, cancelation, and include. The endorsed customers, who have the benefit to get to the proprietor's report, can reliably get to the copies got from the CSP.
4. We give an escalated connection of MB-PMDDP
with a reference plot, which one can procure by growing existing PDP models for dynamic single-copy data.
5. We show the security of our arrangement against plotting servers, and look at a slight change of the proposed plan to recognize corrupted copies. 6. In this work, we don't encode the data to be
outsourced for the going with reasons. In any case, we are overseeing dynamic data, and subsequently if the data report is encoded before outsourcing, changing a touch of the record requires re-encoding the data archive which may not be commendable in useful applications as a result of high count overhead.
7. Second, we are contemplating monetarily
animated CSPs that may try to use less limit than required by the organization contract through cancelation of a few copies of the record. The CSPs have no budgetary favorable position by eradicating only a tad of a copy of the record. 8. Third, and more fundamentally, not in the
slightest degree like erasure codes, duplicating data records over different servers fulfills adaptability which is a basic customer essential in CC structures. A record that is replicated and secured intentionally on various servers – arranged at various geographic regions
System Design
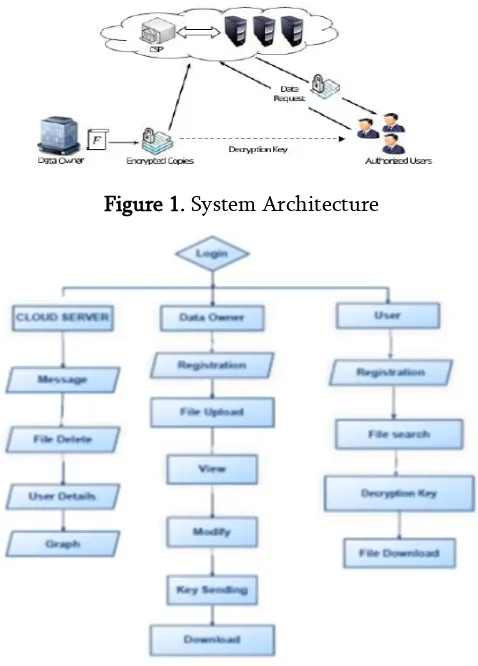
Figure 1. System Architecture
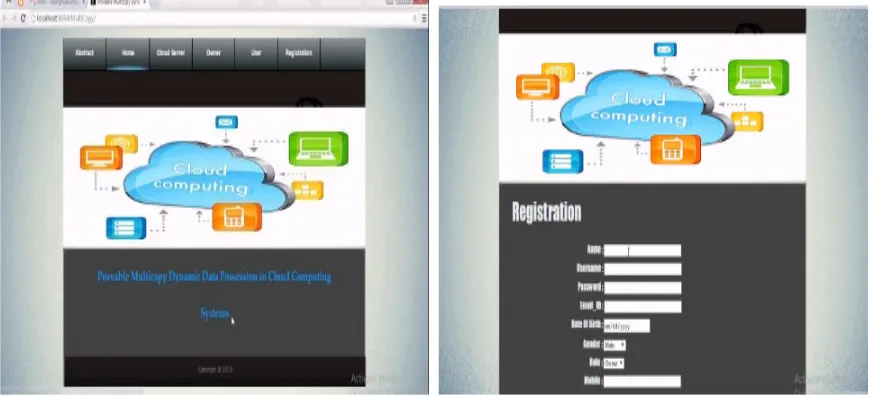
Figure 2. Dataflow Diagram
Cloud Server
The cloud server is a midway substance which stores the encoded records and contrasting documents that are gotten from the data proprietor, and gives data access and request organizations to look customers. Exactly when a request customer sends a watchword to the cloud server, it would reestablish an aggregation of organizing reports in light of particular operations.
Clients Module
A request customer addresses the outsourced reports from the cloud server with following three phases. In the first place, the chase customer gets both the puzzle key and symmetric key from the data proprietor. Second, according to the chase catchphrases, the interest customer uses the puzzle key to deliver trapdoor and sends it to the cloud server.
Last, she gets the organizing report gathering from the cloud server and unscrambles them with the symmetric key.
Classification
The outsourced documents gave by the data proprietor are secured in the cloud server. In case they facilitate the request catchphrases, they are sent to the interest customer. As a result of the security of reports, they should not be identifiable except for by the data proprietor and the affirmed request customers.
The explanation behind testing is to discover goofs. Testing is the route toward endeavoring to locate every conceivable fault or weakness in a work thing. It gives a way to deal with check the convenience of parts, sub social affairs, assemblages and also a finished thing It is the path toward working on programming with the arrangement of ensuring that the Software structure satisfies its requirements and customer wants and does not bomb in an inadmissible way. There are distinctive sorts of test. Each test sort watches out for a specific testing need.
Figure 2. 0wner Login, File Upload
Figure 3. view List of Files, Download
Figure 5. User Request to Owner for File Download, User File Download with Key Received
Figure 6. Cloud View, File Action
Figure 7. Cloud Message, Graph
VI.
CONCLUSION
Outsourcing information to remote servers has turned into a developing pattern for some, associations to lighten the weight of nearby information stockpiling and upkeep. In this work we
where the information proprietor is fit for not just chronicling and getting to the information duplicates put away by the CSP, yet in addition refreshing and scaling these duplicates on the remote servers. To the best of our insight, the proposed conspire is the first to address different duplicates of dynamic information. The communication between the approved clients and the CSP is considered in our plan, where the approved clients can flawlessly get to an information duplicate got from the CSP utilizing a solitary mystery key imparted to the information proprietor. In addition, the proposed scheme bolsters open obviousness, empowers discretionary number of examining, and permits ownership free check where the verifier can confirm the information uprightness despite the fact that he neither has nor recovers the record hinders from the server. Through execution examination and test comes about, we have shown that the proposed MB-PMDDP conspire beats the TB-PMDDP approach got from a class of dynamic single-duplicate PDP models. The TB-PMDDP prompts high stockpiling overhead on the remote servers and high calculations on both the CSP and the verifier sides. The MB-PMDDP conspire altogether diminishes the calculation time amid the test reaction stage which makes it more commonsense for applications where an extensive number of verifiers are associated with the CSP causing a tremendous calculation overhead on the servers. Moreover, it has bring down capacity overhead on the CSP, and in this manner diminishes the expenses paid by the cloud clients. The dynamic piece operations of the guide based approach are finished with less correspondence cost than that of the tree-based approach. A slight adjustment should be possible on the proposed plan to help the element of distinguishing the files of ruined duplicates. The undermined information duplicate can be remade even from an entire harm utilizing copied duplicates on different servers. Through security examination, we have demonstrated that the proposed plot is provably secure.
VII.
REFERENCES
[1].G Ateniese et al , "Prova le data possession at untrusted stores," in Proc 14th ACM Conf. Comput. Commun. Secur. (CCS), New York, NY, USA, 2007, pp. 598-609.
[2].K Zeng, "Pu licly verifia le re ote data integrity," in Proc 10th Int Conf Inf Commun. Secur. (ICICS), 2008, pp. 419-434.
[3].Y. Deswarte, J.-J Quisquater, and A Saidane, "Re ote integrity chec ing," in Proc 6th Working Conf. Integr. Internal Control Inf. Syst. (IICIS), 2003, pp. 1-11.
[4].D L G Filho and P S L M Barreto, "Demonstrating data possession and uncheatable data transfer," IACR (International Association for Cryptologic Research) ePrint Archive, Tech. Rep. 2006/150, 2006.
[5].F. Sebé, J. Domingo-Ferrer, A. Martinez-Balleste, Y. Deswarte, and J.-J. Quisquater, "Efficient re ote data possession chec ing in critical infor ation infrastructures," IEEE Trans. Knowl. Data Eng., vol. 20, no. 8, pp. 1034-1038, Aug. 2008.